
Understanding Healthcare Data Breach Consequences
Data Breach Healthcare Security
Why healthcare is a prime target for cybercriminals? There are a number of factors that interplay that make the …

Data Breach Healthcare Security
Why healthcare is a prime target for cybercriminals? There are a number of factors that interplay that make the …

Understanding healthcare data breaches A healthcare related data breach is when patient information, also known as …
Internal threats cause the majority of data breaches The situation is really that bad. As mentioned, the total number of …

Data Security Best Practices Best Practices
1. Implement A Strong Password Policy Require complex passwords with a minimum length of 12 characters. Do not enforce …

Data Breach Healthcare Security
Why is the Healthcare Industry such an attractive target? Several factors make the healthcare industry particularly …
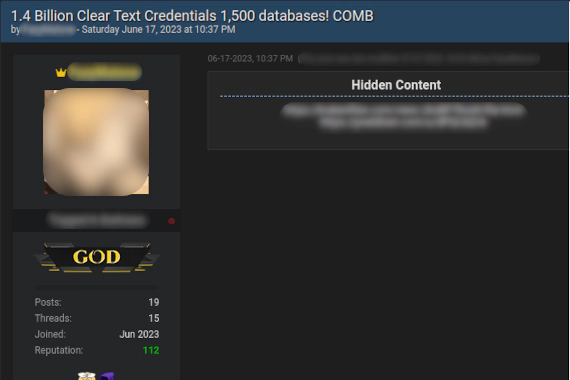
Data Breach Threat Intelligence
What Is A Password Combo List? A password combo list, also known as a combo list, is a collection of username and …

Threat Intelligence Educational Content
Why the Iceberg Metaphor is Wrong The iceberg model suggests a sinister hierarchy, implying that things get …

Dark Web Monitoring Security Tools
Credit Card Fraud on the Dark Web Credit card fraud on the dark web operates quite differently from what many people …

Dark Web Monitoring Educational Content
What Is the Dark Web? The Dark Web is a portion of the internet not indexed by standard search engines. It’s accessible …

Threat Intelligence Educational Content
The Deep Web vs. the Dark Web The internet is far deeper than what you see through typical search engines. The Deep Web …
What is the dark web? The dark web is a “hidden” part of the internet that isn’t indexed by traditional search engines …

Dark Web Monitoring Best Practices
What is Dark Web Monitoring? Dark web monitoring is a service that helps organizations detect if their sensitive …