
Dark Web Monitoring Approaches Explained
What Are the Main Approaches to Dark Web Monitoring? There are three ways security teams monitor the dark web for stolen …

What Are the Main Approaches to Dark Web Monitoring? There are three ways security teams monitor the dark web for stolen …

Dark Web Monitoring Enterprise Security
How Does Enterprise Dark Web Monitoring Work? Dark web monitoring scans criminal sources for data linked to your …
What Are the Breachsense API Endpoints? Breachsense is a dark web monitoring API with 9 REST endpoints, each covering a …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
February 2026 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. …

Dark Web Monitoring Data Security Compliance
How does Breachsense handle monitoring data? Breachsense collects data from dark web sources and indexes it so you can …

How Do You Onboard a New Client? Getting a new client into your dark web monitoring workflow starts before you touch any …

Why Do You Need Alert-Specific Response Playbooks? A credential leak and a ransomware victim announcement are very …

What Dark Web Sources Does Breachsense Monitor? Your credentials could be for sale right now. You’d never know unless …
Dark Web Monitoring Compromised Credentials Group-IB Threat Intelligence Credential Monitoring
What Does Group-IB Do? Group-IB is a cybersecurity company that sells a suite of products under their Unified Risk …

Dark Web Monitoring Threat Intelligence Cybersecurity Glossary Breach Detection
What Does This Page Cover? Security teams deal with dozens of specialized terms when evaluating dark web monitoring …

Digital Risk Protection Dark Web Monitoring Compromised Credentials Threat Intelligence Credential Monitoring
What Does Digital Risk Protection Actually Cover? Vendors use “digital risk protection” loosely. Gartner and Forrester …
Dark Web Monitoring Compromised Credentials Flare Threat Intelligence Credential Monitoring
What Does Flare Do? Flare is a threat exposure management platform. They monitor dark web sources and clear web …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
January 2026 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. …

Dark Web Monitoring Compromised Credentials SpyCloud Threat Intelligence Credential Monitoring
What Does SpyCloud Do Well? SpyCloud’s dark web monitoring focuses on extracting stolen credentials from third-party …

Authentication Dark Web Monitoring Credential Monitoring Security Tools
Top 10 Account Takeover Solutions at a Glance Platform Category Best For Breachsense Credential Intelligence Dark web …

Dark Web Monitoring Compromised Credentials DarkOwl Threat Intelligence Credential Monitoring
What Does DarkOwl Do? DarkOwl is a darknet data platform. They collect content from across the dark web and make it …

Dark Web Monitoring Threat Intelligence Credential Monitoring Security Research
What Is a Dark Web Market? When your credentials get stolen, they often end up for sale on a dark web market within …

Digital Risk Protection Threat Intelligence Dark Web Monitoring Cybersecurity Platforms Security Tools
What Are the Best Digital Risk Protection Platforms? Platform Best For Key Strength Breachsense Security teams, …

Brand Protection Phishing Detection Dark Web Monitoring Counterfeit Protection Security Tools
What Are the Best Brand Protection Platforms? Brand protection software covers a wide range of threats. Some platforms …

Dark Web Monitoring Best Practices
What Is Dark Web Monitoring for Business? Most security teams understand dark web monitoring in theory. The execution is …

Dark Web Monitoring Threat Intelligence
What Is Dark Web Threat Intelligence? Your employees’ credentials are probably for sale right now. The question is …

Dark Web Monitoring Threat Intelligence Cybersecurity Data Breach Detection
Which Dark Web Monitoring Services Made the List? Service Best For Key Strength Breachsense Security teams, MSPs, …

Dark Web Monitoring Security Tools
Stolen credentials remain the number one initial access vector. The right dark web monitoring tool catches leaked …

Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
2025 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. Breachsense …
Email Security Dark Web Monitoring
What Does It Mean if Your Email Is Found on the Dark Web? Finding your email on the dark web is more common than you’d …
Dark Web Monitoring Security Operations ROI
What Does Dark Web Monitoring Actually Provide? Before evaluating whether monitoring is worth it, let’s be clear about …

Dark Web Monitoring Threat Intelligence Security Operations
What Is Dark Web Monitoring? Your credentials could be for sale right now. You’d never know unless you’re actively …

Digital Risk Protection DRP Security Dark Web Monitoring Threat Intelligence Cybersecurity
What is Digital Risk Protection? Most security teams watch their internal networks. DRP platforms watch everywhere else. …

Dark Web Monitoring Threat Intelligence SocRadar Digital Risk Protection Credential Monitoring
What Does SocRadar Do? SocRadar markets itself as an “Extended Threat Intelligence” platform. That’s their branding for …

Dark Web Monitoring ZeroFox Digital Risk Protection Compromised Credentials Credential Monitoring
What Does ZeroFox Do? ZeroFox is a digital risk protection platform that monitors external threats across social media …
Threat Intelligence Recorded Future Dark Web Monitoring Compromised Credentials Credential Monitoring
What Does Recorded Future Do? Recorded Future is an enterprise threat intelligence platform providing broad coverage …

Dark Web Monitoring Compromised Credentials SpyCloud Threat Intelligence Credential Monitoring
What Does SpyCloud Do? SpyCloud is an enterprise-focused platform that detects stolen credentials to prevent account …

Supply Chain Security Third-Party Risk Data Breaches Vendor Risk Management Dark Web Monitoring
What Is a Supply Chain Attack? Your vendors have keys to your kingdom. When attackers steal those keys, they walk right …

Vendor Risk Management Third-Party Risk Supply Chain Security Dark Web Monitoring
What Is Vendor Risk Management? Your vendors have access to your data. When they get breached, your data gets exposed …

Credential Stuffing Account Takeover Compromised Credentials Dark Web Monitoring Authentication Security
What Is Credential Stuffing? Password reuse creates a massive security hole. When you use the same password on multiple …
Dark Web Monitoring Threat Intelligence Security Tools OSINT
What Is a Dark Web Search Engine? The dark web (sometimes called the black web or darknet) operates on a completely …
Dark Web Monitoring MSP Cybersecurity Tools Credential Monitoring Managed Service Providers
Platform Best For Key Strength Breachsense API-first MSPs Multi-tenant API, infostealer coverage ID Agent Dark Web ID …
Infostealer Malware Credential Theft Dark Web Monitoring Cybersecurity
What Is Infostealer Malware? Infostealer malware is the quiet threat most security teams underestimate. Infostealer …

Ransomware Detection Threat Intelligence Dark Web Monitoring Credential Monitoring Cybersecurity
What Is Ransomware Detection? Most organizations discover ransomware when files start disappearing or ransom notes …

Data Breach Detection Dark Web Monitoring Credential Monitoring Cybersecurity Tools Threat Intelligence
What Are Data Breach Detection Tools? Most security tools watch your internal network. Breach detection tools watch …

Threat Intelligence Dark Web Monitoring Security Tools
What Is Cyber Threat Monitoring? Security teams can’t protect what they can’t see. Cyber threat monitoring gives you …
Threat Intelligence Dark Web Monitoring Security Tools CTI
What Are Cyber Threat Intelligence Tools? CTI tools provide security teams with information about threats targeting …

Data Breach Prevention Credential Monitoring Dark Web Monitoring Cybersecurity
What Is Data Breach Prevention? Most security tools watch for attackers inside your network. By then, it’s often too …

Dark Web Monitoring Threat Intelligence Credential Monitoring
What Is Deep Web Monitoring? Most security discussions focus on the dark web. But threats often appear elsewhere first. …

Dark Web Monitoring Healthcare Security Data Breach HIPAA Compliance
What Is Dark Web Monitoring for Healthcare? Healthcare organizations face unique cybersecurity challenges. Patient data …
Dark Web Monitoring Credential Monitoring Data Breach
What Are Leaked Emails? Most security teams think about leaked emails as a consumer problem. Check your personal email …

Credential Monitoring Dark Web Monitoring Data Breach Security Tools
What Are Dark Web Monitoring Tools? Dark web monitoring tools scan criminal sources for exposed passwords linked to your …

Phishing Account Takeover Dark Web Monitoring
What Are Impersonation Attacks? Most phishing emails are easy to spot. Bad grammar, suspicious links, requests from …

Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends Infostealer
What Are the Current Ransomware Trends? The ransomware landscape looks different than most headlines suggest. Reported …

Credential Monitoring Dark Web Monitoring Data Breach
Why Should Security Teams Check Employee Credentials? Most security teams focus on blocking attacks. But what happens …
Credential Monitoring Dark Web Monitoring Data Breach
What Are Compromised Credentials? Compromised credentials are authentication data that attackers have stolen. This …

Credential Monitoring Data Breach Dark Web Monitoring
Where Do Leaked Corporate Credentials Appear? Corporate credentials leak through multiple channels. Security teams need …
Indicators of Compromise IOC Threat Intelligence Dark Web Monitoring Cybersecurity Breach Detection
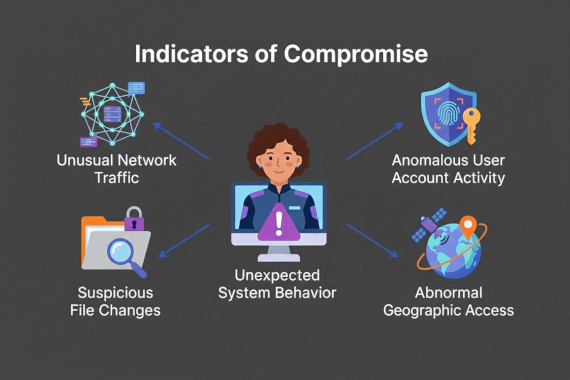
IOCs work. But they work after the fact. By the time you find a malicious file hash or C2 beacon, attackers have already …

Digital Risk Monitoring Digital Risk Management Third Party Risk Threat Intelligence Dark Web Monitoring External Threats
External actors cause 62% of data breaches globally (71% in EMEA), but most companies only watch their internal …

Digital Risk Management Dark Web Monitoring Cyber Risk Third-Party Risk
What is Digital Risk Management? Digital risk management is watching for threats outside your network. Not just what’s …

Dark Web Monitoring Threat Intelligence Best Practices
How is threat intelligence collected? Threat intelligence collection isn’t some magical process where data just appears …

Dark Web Monitoring Threat Intelligence Best Practices
What is Threat Intelligence Management? If you’ve been in security for any length of time, you’ve probably been drowning …

Cyber Threat Intelligence Dark Web Monitoring
Cyber Threat Intelligence Explained Cyber Threat Intelligence (CTI) is the process of collecting, analyzing, and sharing …

Dark Web Monitoring Security Tools
Credit Card Fraud on the Dark Web Credit card fraud on the dark web operates quite differently from what many people …

Dark Web Monitoring Educational Content
What Is the Dark Web? The Dark Web is a portion of the internet not indexed by standard search engines. It’s accessible …

Dark Web Monitoring Identity Theft
What is the dark web? The dark web refers to a 'hidden' part of the internet that can only be accessed using specialized …

Data Security Best Practices Dark Web Monitoring
What is big data security? Big data security is a set of security measures, tools, and practices that are used to …