Deep Web vs Dark Web: What's the Difference?
Learn how the deep web and dark web differ and why your security team needs to monitor both.
• The deep web is anything not indexed by search engines. You use it every day when you check email or log into your bank. The dark web requires Tor and hosts criminal marketplaces.
• Stolen credentials appear on deep web sources like Telegram channels hours after infection. They don’t reach dark web markets for days or weeks.
• Accessing the dark web isn’t illegal. Buying stolen data is. Security researchers and monitoring vendors access it legally as part of their work.
• If you only scan dark web marketplaces, you’re missing where most stolen data first surfaces. You need deep and dark web monitoring together.
The deep web makes up roughly 95% of the internet. The dark web is a tiny fraction of that. But it’s where stolen credentials end up listed for purchase.
Security teams that confuse these terms end up with blind spots. If you only monitor dark web marketplaces, you’ll miss the Telegram channels and private forums where stolen data appears first.
The difference between deep web and dark web isn’t just academic. It determines which sources you monitor and how much time you have to respond.
This guide breaks down the difference between deep web and dark web, what lives on each layer, and what your security team should monitor.
What Is the Difference Between the Deep Web and Dark Web?
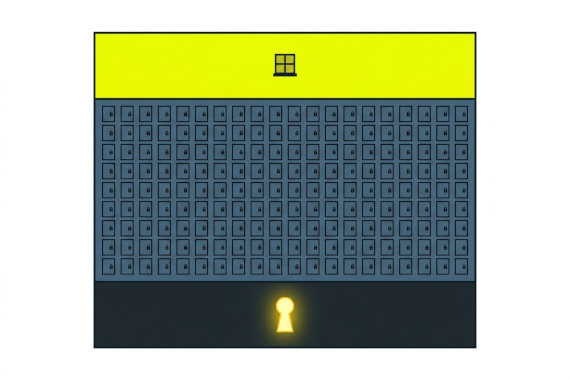
The internet has three layers. Each one works differently and carries different risks for your organization.
The surface web is what search engines index. Google can find and display this content. It makes up roughly 5% of the total internet.
The deep web is any internet content not indexed by search engines. It includes email inboxes, banking portals, and anything behind a login page. It makes up roughly 95% of the internet and most of it is completely legitimate.
The dark web is a small subset of the deep web that requires specialized software to access. Users need the Tor browser to reach .onion sites. Criminal marketplaces and ransomware leak sites operate here.
Here’s how the three layers compare:
| Surface Web | Deep Web | Dark Web | |
|---|---|---|---|
| Access | Standard browser | Login credentials | Tor browser |
| Size | ~5% of internet | ~95% of internet | <1% of internet |
| Content | Public websites, news | Email, banking, intranets | Marketplaces, forums, leak sites |
| Indexed | Yes | No | No |
| Legal | Yes | Yes | Legal to access, illegal to buy stolen data |
| Examples | Google, Wikipedia | Gmail, corporate intranet | Dark web markets, ransomware sites |
| Monitoring need | Brand mentions | Credential leaks, access broker listings | Active sales, breach confirmations |
The key distinction for security teams: threats move through these layers. Stolen credentials might appear in a Telegram channel (deep web) within hours of an infostealer infection. Days later, the same data shows up on a dark web marketplace. If you only watch the dark web, you’re catching threats late.
What Is the Deep Web?
You use the deep web every day. Every time you log into your email, check your bank account, or access your company’s intranet, you’re on the deep web.
The deep web exists because not everything should be publicly searchable. Medical records and financial data sit behind authentication for good reason. Search engines can’t crawl past login pages, so this content stays out of Google’s index.
Common deep web content includes:
- Email accounts:Gmail, Outlook, corporate email
- Banking portals:online banking and investment accounts
- Corporate systems:intranets, HR portals, internal wikis
- Medical records:patient portals and health databases
- Subscription content:paywalled news sites and research databases
The deep web itself isn’t dangerous. But it’s also where attackers share stolen data. Telegram channels and private forums live on the deep web. That’s why deep web monitoring matters for security teams.
What Is the Dark Web?
The dark web requires the Tor browser to access. Tor routes your traffic through multiple encrypted relays, hiding your IP address and location. Sites use .onion domains that standard browsers can’t reach.
The dark web is a network of websites accessible only through anonymizing software like Tor. It hosts criminal marketplaces where stolen data is sold and ransomware gang leak sites. It also hosts legitimate privacy tools used by journalists and activists.
Not everything on the dark web is illegal. Journalists use it to communicate with sources. Activists in authoritarian countries use it to organize. The BBC and other news organizations run .onion versions of their sites.
But the dark web is best known for criminal activity. Dark web markets sell stolen credentials and counterfeit documents. Ransomware gangs post stolen data on leak sites to pressure victims into paying. Hacker forums trade exploits and network access.
The anonymity that protects journalists also protects criminals. That’s what makes the dark web a security concern for your organization.
What Data Gets Sold on the Dark Web?
Your employees’ credentials are the most common item for sale. The Verizon 2025 Data Breach Investigations Report found that stolen credentials were the most common initial access vector, used in 22% of breaches.
Here’s what attackers sell:
- Stolen credentials:usernames and passwords from breaches and stealer logs. Corporate email passwords are especially valuable.
- Credit card data:card numbers and CVVs. Often sold in bulk.
- Medical records:patient data that can be used for insurance fraud. Worth more than credit cards because you can’t change your medical history.
- Corporate network access:VPN credentials or admin accounts sold by initial access brokers. Ransomware operators buy these to get into your network.
Most of this data starts somewhere else. Infostealer malware grabs credentials from infected devices. The stolen data gets shared in Telegram channels (deep web) first. Eventually it ends up packaged and listed on dark web marketplaces.
Is It Legal to Access the Deep Web and Dark Web?
You access the deep web every time you check email. It’s completely legal and a normal part of using the internet.
The dark web is also legal to access. The Tor browser is legal software maintained by a nonprofit. Downloading and using it isn’t a crime in most countries.
What’s illegal is what you do on the dark web. Buying stolen credentials, purchasing drugs, or downloading illegal content are all crimes regardless of where you do it.
Security professionals access the dark web legally every day. Researchers monitor dark web forums to track threats. Compromised credential monitoring vendors scan dark web sources to find your organization’s exposed data. Law enforcement uses it for investigations.
How Do Security Teams Monitor the Deep Web and Dark Web?
Monitoring both layers gives you coverage across the entire lifecycle of stolen data.
Deep and dark web monitoring work together but cover different sources. Deep web monitoring scans Telegram channels and stealer log repositories where stolen data first appears. Dark web monitoring watches criminal marketplaces and ransomware leak sites where data is actively sold.
The timing difference matters. Credentials from an infostealer infection might appear in a Telegram channel within hours. The same data won’t show up on a dark web marketplace for days or weeks. If you only monitor the dark web, you’ve lost your fastest response window.
Here’s what a typical monitoring workflow looks like:
- Credential appears in a stealer log on a Telegram channel (deep web)
- Your monitoring platform matches it against your corporate domains
- You get an alert with context about what was exposed and where
- You reset the password before anyone buys or uses the credential
- The same credential later appears on a dark web marketplace, but you’ve already closed the gap
Dark web monitoring confirms what’s actively being sold. Deep web monitoring catches it earlier. You need both.
How Can You Tell If Your Data Is on the Dark Web?
You won’t find your data by browsing dark web sites yourself. It’s dangerous and inefficient. Use a scanning service instead.
A dark web scan checks if your organization’s credentials appear on dark web marketplaces and in stealer logs. You’ll see which email addresses are exposed and what passwords leaked.
A one-time scan shows you what’s already out there. But credentials leak continuously. New breaches happen every day. Infostealer infections produce fresh stealer logs around the clock.
That’s why continuous monitoring beats one-time scans. You want to know the moment a new credential appears, not weeks later during a scheduled check. Learn more about how scanning works in our guide on what a dark web scan is.
Conclusion
The deep web and dark web are different layers with different risks. The deep web is where stolen data first appears. The dark web is where it gets sold. Your security team needs to watch both.
Check your organization’s dark web exposure or book a demo to see how Breachsense monitors both the deep web and dark web for your leaked credentials.