Third-Party Data Breaches: What They Are and How to Prevent Them
What Is a Third-Party Data Breach? A third-party data breach happens when attackers access your data through an external …
What Is a Third-Party Data Breach? A third-party data breach happens when attackers access your data through an external …

Data Breach Healthcare Security
Why Is Healthcare the Most Expensive Industry for Data Breaches? Healthcare has topped IBM’s cost rankings for 14 …

Authentication Data Breach Credential Monitoring
What Does It Mean When Your Passwords Are Leaked? Your credentials can leak without your company doing anything wrong. A …

Data Breach Detection Techniques
What Types of Data Get Leaked in a Breach? If you’re searching for your company’s breached data, you need to know what …
Insider Threat Data Breach Data Loss Prevention
What Is an Insider Threat? An insider threat is a current or former employee, contractor, or business partner who …

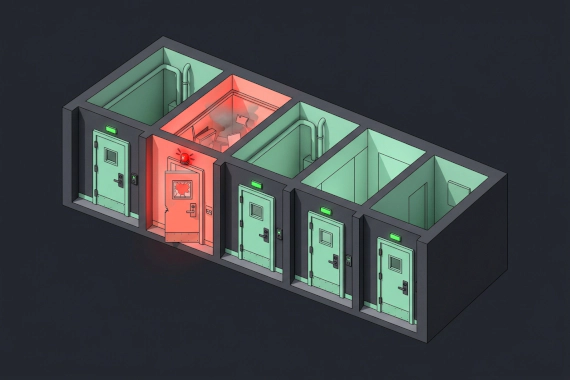
Step 1: How Do You Contain the Breach? The first hours after detection set the trajectory for everything that follows. …
Step 1: Who’s on Your Response Team? When a breach hits, the first question everyone asks is “who’s handling this?” If …

What Is Data Breach Protection? There’s no single product you can buy that stops breaches. Protection is a stack of …

What Is a Data Breach Notification? When personal data gets compromised, you don’t just have a security problem. You …
How Much Does a Data Breach Cost? The financial consequences of a data breach go far beyond the initial incident …
What Is Data Breach Mitigation? You can’t prevent every breach. But you can control how much damage one causes. Data …

Data Breach Cyberattack Trends
What Are the Main Types of Data Breaches? Not all breaches look the same. The method and the defense are different for …

What Is Human Error in Cybersecurity? You can invest in firewalls and endpoint detection. But when an employee clicks a …

What Do the Latest Breach Statistics Tell Us? These numbers aren’t just data points. Each one represents a decision that …

What Does Data Breach Insurance Cover? Traditional business insurance won’t help you after a cyber attack. General …

Data Breach Cyberattack Trends
What is a data breach? Data breach is a security incident where an unauthorized party accesses sensitive, protected, or …

What is data breach compliance? You’ll see this term in vendor contracts and regulatory filings. Here’s what it actually …

What Is a Data Leak? A data leak happens when sensitive information gets exposed without anyone intending it to. No …

How Much Does a Data Breach Cost? The global average cost of a data breach dropped to $4.44 million in 2025, down from …

Credential Monitoring Dark Web Monitoring Data Breach
Why Should Security Teams Check Employee Credentials? Most security teams focus on blocking attacks. But what happens …

1. Yahoo Date: August 2013 Impact: 3 billion records Yahoo holds the record for the largest data breach in history, and …

Data Breach Healthcare Security
Why healthcare is a prime target for attackers? Several factors make the healthcare sector particularly vulnerable to …

What Should You Do Immediately After a Data Breach? You’ll hear “data breach response” a lot in the next few sections. …
Data Breach Credential Monitoring
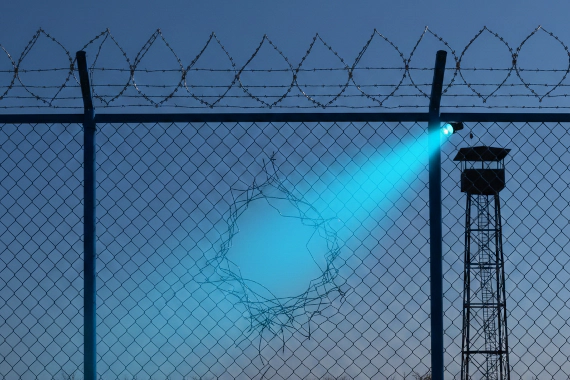
What Is Data Breach Detection? Most companies don’t know they’ve been breached. Not for weeks. Often not even for …

What Is a Data Breach? Security teams deal with data breaches constantly, but the definition matters for legal and …

What Happened in the Target Data Breach? The Target data breach of 2013 remains one of the most studied cyberattacks in …

Data Breach Incident Response Credential Theft
What Is Data Theft? When attackers break in, they’re not just looking around. They’re taking what they came for. Unlike …

What Happened in the Home Depot Data Breach? The Home Depot data breach was one of the largest retail security incidents …
Data Breach Threat Intelligence
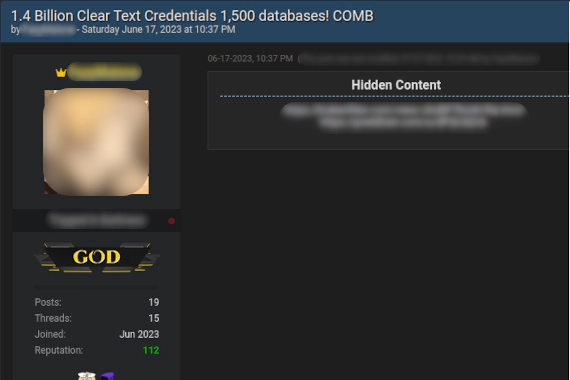
What Is A Password Combo List? Combo List: A file containing username and password pairs collected from data breaches …
What Happened in the Equifax Data Breach? The Equifax breach started with a web application vulnerability that had been …
Data Breach Case Studies Telecom Security Network Security
What Happened in the T-Mobile Data Breaches? T-Mobile has disclosed at least seven significant data breaches since 2018. …
Data Breach Case Studies Cloud Security AWS Bank Data Breach Capital One Breach
What Happened in the Capital One Data Breach? The Capital One data breach exposed personal information from 106 million …

Data Breach Case Studies M&A Security Hospitality Hotel Data Breach
What Happened in the Marriott Data Breach? The Marriott data breach exposed personal information belonging to …
Data Breach Case Studies Supply Chain Security Third-Party Risk
What Happened in the SolarWinds Data Breach? The SolarWinds data breach represents the most damaging supply chain attack …

Data Breach Case Studies Credential Stuffing Genetic Data
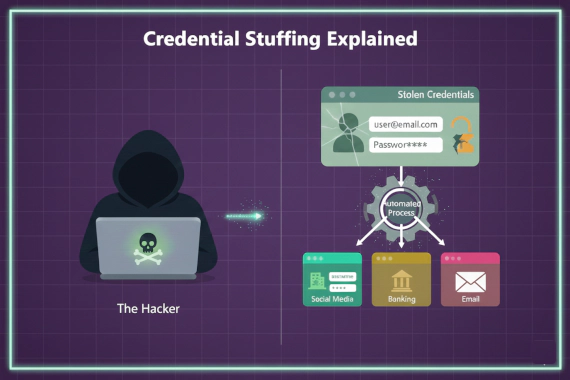
What Happened in the 23andMe Data Breach? The 23andMe data breach exposed genetic profiles belonging to approximately 7 …

Data Breach Case Studies Session Hijacking Identity Security MFA Bypass
What Happened in the Okta Data Breach? Okta serves over 18,000 customers as a critical identity infrastructure provider. …

Data Breach Case Studies Healthcare Security Ransomware Credential Theft
What Happened in the Change Healthcare Breach? On February 21, 2024, Change Healthcare detected ransomware deployed …

Data Breach Case Studies Password Security Credential Theft
What Happened in the LastPass Data Breach? The LastPass data breach stands as one of the most consequential security …
Threat Intelligence Data Breach Credential Security
Breach intelligence is a specialized form of threat intelligence focused on collecting and analyzing information about …

Every business stores sensitive data. Customer records, employee credentials, financial information. When unauthorized …
Dark Web Monitoring Credential Monitoring Data Breach
What Are Leaked Emails? Most security teams think about leaked emails as a consumer problem. Check your personal email …

Credential Monitoring Dark Web Monitoring Data Breach Security Tools
What Are Dark Web Monitoring Tools? Dark web monitoring tools scan criminal sources for exposed passwords linked to your …
Account Takeover Credential Monitoring Data Breach
What Is Credential Stuffing? Most people hear “credential stuffing” and think it’s just another brute force attack. It’s …
Credential Monitoring Dark Web Monitoring Data Breach
What Are Compromised Credentials? Compromised credentials are authentication data that attackers have stolen. This …

Credential Monitoring Data Breach Dark Web Monitoring
Where Do Leaked Corporate Credentials Appear? Corporate credentials leak through multiple channels. Security teams need …

Why Is Healthcare the Most Targeted Industry? When a retailer gets breached, you cancel a credit card. When a hospital …

Initial Response (First 24 Hours) During the first 24 hours after identifying a breach, security teams need to identify …

What is a data breach? A data breach occurs when sensitive information is accessed by unauthorized individuals. There …

The impact of hybrid work on cybersecurity Having employees work both remotely and in the office has significantly …

How Small Business Data Breaches Typically Occur FACT: There are countless ways for hackers and cybercriminals to gain …

Data Breach Trust and Reputation
Data Breaches Damage Brand Reputation Data breaches can severely undermine the trust customers place in an …

Poor Password Management is a Leading Cause of Data Breaches Naturally, the issue isn’t just that we don’t protect our …