Check your dark web exposure
Enter your domain name or email address into our dark web scanner to identify threats to your organization like employees with malware infected devices, stolen session cookies and credentials leaked in combo lists or third-party breaches.
No Data Breach Detected
But You’re Not Exactly in the Clear
Prevent Future Data Breaches With Breachsense
- Continuously monitor the open, deep, and dark web for mentions of your company, personal staff information, and other important data.
- Detect data breaches in real-time and prevent cyberattacks before they happen.
- Uncover mentions of your VIPs, executive staff, or clients on private ransomware forums and mitigate threats preemptively.
Data Breach Detected
It’s Time to Act
Secure Your Breached Accounts
- Reset Account Credentials for all compromised accounts.
- Enable 2-Factor Authentication to prevent attackers from using leaked passwords.
- Use Unique & Strong Passwords. Make this a company-wide practice.
- Train Your Staff on Security Best Practices. Actively train your employees on why cybersecurity is important and how they can prevent breaches.
- Always Use a Password Manager. Make this a company standard.
- Continuously Monitor for Data Breaches. Even if you do everything right, there’s still a risk of human error. Breachsense allows you to uncover data breaches in real time.
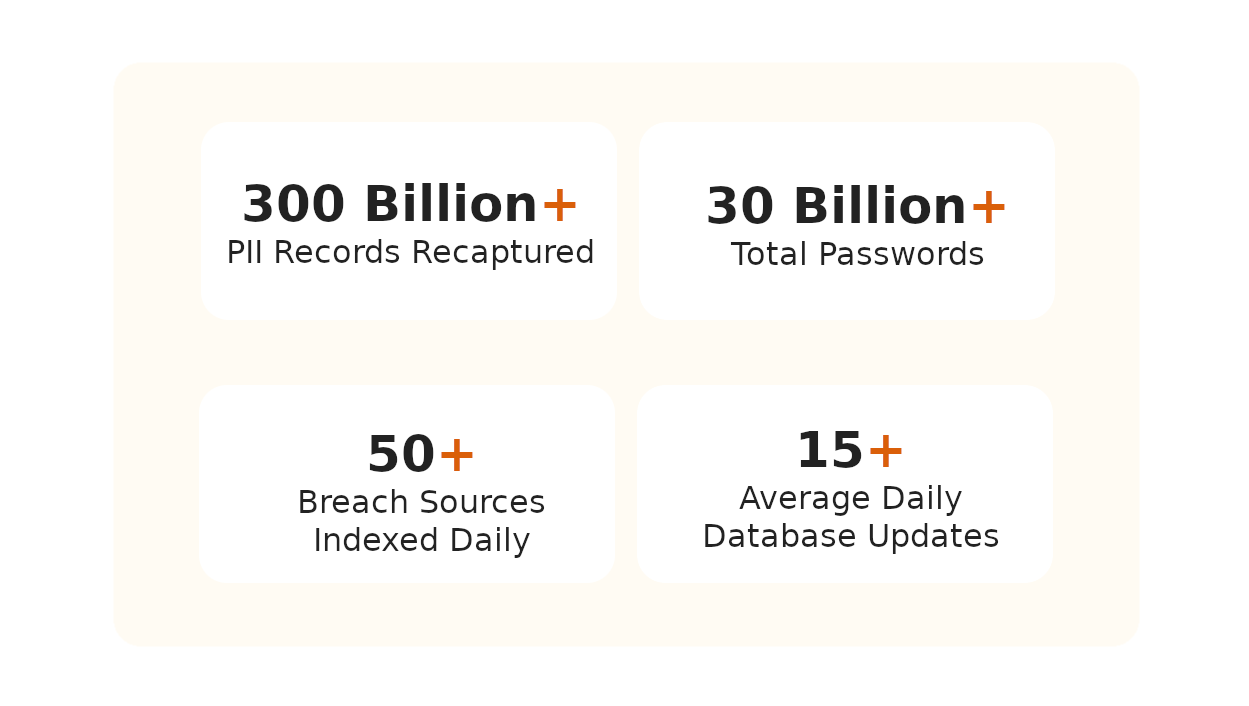
Why Use Breachsense
Our data breach checker provides actionable threat intelligence to prevent ransomware, account takeover, and online fraud.
Early Data Breach Detection and Response
Easy Integration with Your CTI Toolset
Instant Alerts for Quick Incident Response
What is the dark web?
It requires specialized software, like Tor, to access, allowing users to browse anonymously.
It’s primarily known for illegal activities such as the sale of stolen data, drugs, and hacking services.
Due to its anonymous nature, the dark web attracts cybercrime, thus it’s critical to monitor for potential threats.
Why get a dark web scan?
Early detection enables you to take immediate action to secure your accounts and prevent identity theft or fraud.
Thus, regular dark web scans are a proactive measure that helps reduces risks and enables you to mitigate risks before they’re exploited.
What causes data breaches?
- Stolen or leaked credentials
- Misconfigured Security Settings
- Accidental Sharing of sensitive information with the wrong recipient
- Third-party vendors with access to your data who experience a breach
- Vulnerable websites or applications
- Social engineering / phishing attacks
- Disgruntled or careless employees who intentionally or accidentally share sensitive data
- Lost of stolen devices which contain sensitive data
- Improper disposal of old devices and storage media which contain confidential information

Frequently Asked Questions
What is a dark web scan?
A dark web scan, or dark web test is a process where specialized tools search the dark web for your organization’s information, such as stolen usernames, passwords, internal company documents, or other sensitive data. The dark web is a hidden part of the internet where illegal activities often take place, and data breaches are commonly sold or shared there.
Can I check if my information is on the dark web?
Yes, you can check if your details are on the dark web using specialized data breach tools or services. An email dark web check scans stealer logs, dark web markets and third party breaches for your email address. When the breach monitoring tool finds a match, it will alert you so you can take steps to protect your account.
MORE INFO: How to find data breaches
What does a data breach scanner do?
A data breach scanner searches the internet and dark web for your corporate information that might have been exposed in a data breach. A data breach check scans telegram channels, paste sites and websites where stolen data is often shared or sold. If it finds your information, it sends you an alert. Early data breach detection enables you to mitigate the risk before bad actors exploit it.
How do I delete my data from the dark web?
Deleting your data from the dark web is extremely difficult because once it’s there, it’s often copied and shared across multiple sites. However, you can protect yourself by changing your employee’s leaked passwords, enabling two-factor authentication, using a password manager, monitoring the internet for potential phishing domains, and monitoring the dark web for your organization’s leaked or stolen data.
How do dark web scans work?
Dark web scans search the hidden parts of the internet for your organization’s data, such as email addresses, passwords and proprietary files. When relevant data is found, you’ll receive an alert with details, allowing you to take action, like updating passwords or monitoring accounts. The scans run continuously, helping you stay informed about new threats and protect your assets over time.
Are your passwords on the dark web?
If your passwords have been exposed in a data breach, stealer logs, or a combo list, they could be circulating on the dark web. Use a data breach checker to scan the dark web for your compromised passwords. Our dark web scan monitors dark net forums, marketplaces, third party breaches, combo lists, and infostealer logs for credentials associated with your organization. We alert you when your employees’ passwords are detected, enabling your security team to take immediate action.