
Data Breach Response Checklist: 5 Steps to a Data Breach Response Plan
Step 1: How Do You Contain the Breach? The first hours after detection set the trajectory for everything that follows. …

Step 1: How Do You Contain the Breach? The first hours after detection set the trajectory for everything that follows. …
Step 1: Who’s on Your Response Team? When a breach hits, the first question everyone asks is “who’s handling this?” If …
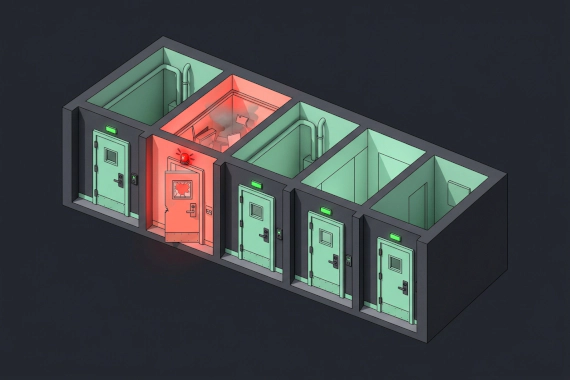
What Is Data Breach Mitigation? You can’t prevent every breach. But you can control how much damage one causes. Data …

What Should You Do Immediately After a Data Breach? You’ll hear “data breach response” a lot in the next few sections. …

Data Breach Incident Response Credential Theft
What Is Data Theft? When attackers break in, they’re not just looking around. They’re taking what they came for. Unlike …
Incident Response Security Operations Security Metrics
MTTR (Mean Time To Respond) measures the average time it takes for a security team to contain and remediate an incident …

Why Do You Need a Ransomware Response Plan? A ransomware attack at 2am is not the time to figure out who makes …

Malware Incident Response Infostealers
What Is Malware Incident Response? Malware incident response is how your security team detects, contains, and recovers …