
Best Dark Web Monitoring Services for Business Compared
Dark Web Monitoring Threat Intelligence Cybersecurity Data Breach Detection
Which Dark Web Monitoring Services Made the List? Service Best For Key Strength Breachsense Security teams, MSPs, …

Dark Web Monitoring Threat Intelligence Cybersecurity Data Breach Detection
Which Dark Web Monitoring Services Made the List? Service Best For Key Strength Breachsense Security teams, MSPs, …

Digital Risk Protection DRP Security Dark Web Monitoring Threat Intelligence Cybersecurity
What is Digital Risk Protection? Most security teams watch their internal networks. DRP platforms watch everywhere else. …

Dark Web Tor Browser Privacy Anonymity Cybersecurity
What Is the Dark Web? The dark web is a small encrypted portion of the internet requiring special browsers to access. It …
Infostealer Malware Credential Theft Dark Web Monitoring Cybersecurity
What Is Infostealer Malware? Infostealer malware is the quiet threat most security teams underestimate. Infostealer …

Ransomware Detection Threat Intelligence Dark Web Monitoring Credential Monitoring Cybersecurity
What Is Ransomware Detection? Most organizations discover ransomware when files start disappearing or ransom notes …

Data Breach Prevention Credential Monitoring Dark Web Monitoring Cybersecurity
What Is Data Breach Prevention? Most security tools watch for attackers inside your network. By then, it’s often too …

Zero-Day Exploits Vulnerability Management Threat Intelligence Cybersecurity Enterprise Security
What Is a Zero-Day Exploit? A zero-day exploit takes advantage of a software vulnerability that nobody knows about yet. …

Every business stores sensitive data. Customer records, employee credentials, financial information. When unauthorized …
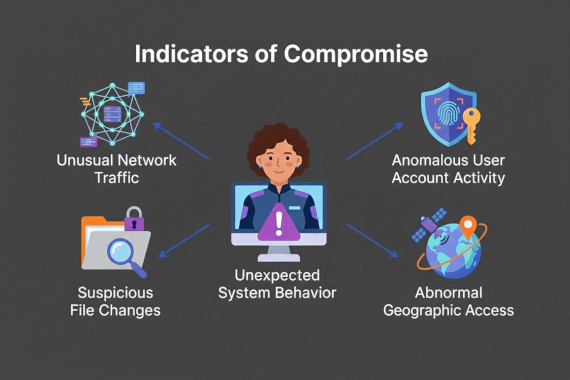
Indicators of Compromise IOC Threat Intelligence Dark Web Monitoring Cybersecurity Breach Detection
IOCs work. But they work after the fact. By the time you find a malicious file hash or C2 beacon, attackers have already …

Attack Surface Management Vulnerability Management EASM Security Operations Cybersecurity
What Is Vulnerability Management? Vulnerability management is the foundation of traditional security programs. You scan …

Attack Surface Management EASM Security Assessment Vulnerability Management Cybersecurity
What Is Attack Surface Assessment? Security teams protect what they know about. The problem is they don’t know about …

Threat Intelligence Cybersecurity Enterprise Security
Why Threat Intelligence Platforms Matter Now Traditional firewalls can’t protect against stolen passwords. VPNs don’t …
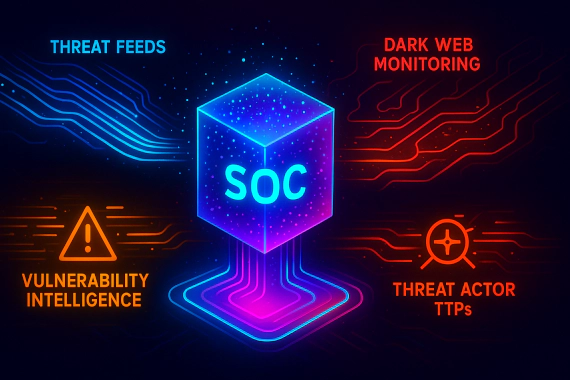
Threat Intelligence Cybersecurity External Threat Intelligence CTI
What is External Threat Intelligence? External threat intelligence is threat data collected from outside your …

Threat Intelligence Cybersecurity CTI Security Operations
What Do We Mean by Levels of Threat Intelligence? The term “levels” indicates hierarchical progression from micro to …

Threat Intelligence Cybersecurity CTI Security Operations
What is the Threat Intelligence Lifecycle? The threat intelligence lifecycle is a six-phase iterative framework that …