
What Are Compromised Credentials? Detection & Response
Credential Monitoring Dark Web Monitoring Data Breach
What Are Compromised Credentials? Compromised credentials are authentication data that attackers have stolen. This …

Credential Monitoring Dark Web Monitoring Data Breach
What Are Compromised Credentials? Compromised credentials are authentication data that attackers have stolen. This …
Ransomware Detection Threat Intelligence Dark Web Monitoring Credential Monitoring Cybersecurity
What Is Ransomware Detection? Most companies discover ransomware when files start disappearing or ransom notes appear. …

Authentication Data Breach Credential Monitoring
What Does It Mean When Your Passwords Are Leaked? Your credentials can leak without your company doing anything wrong. A …

Credential Monitoring Dark Web Monitoring Data Breach
Why Should Security Teams Check Employee Credentials? Most security teams focus on blocking attacks. But what happens …

Ransomware Monitoring Dark Web Monitoring Threat Intelligence Credential Monitoring
What Is Ransomware Monitoring? You’ll see “ransomware monitoring” used loosely across vendor marketing. Here’s what it …

Dark Web Monitoring Recorded Future Threat Intelligence Compromised Credentials Credential Monitoring
How Does Recorded Future Handle Dark Web Monitoring? Recorded Future is a threat intelligence platform that includes …
Dark Web Monitoring Flare Threat Intelligence Credential Monitoring Threat Exposure Management
What Does Flare Do Well? Flare built their platform around Threat Exposure Management. They combine dark web monitoring …
Dark Web Monitoring Group-IB Threat Intelligence Credential Monitoring Digital Risk Protection
What Does Group-IB Do Well? Group-IB is a cybersecurity company that sells a suite of products under their Unified Risk …

Credential Monitoring Dark Web Monitoring Compromised Credentials Threat Intelligence Infostealer Detection
What Does Credential Monitoring Actually Cover? “Credential monitoring” means different things depending on the vendor. …
Dark Web Monitoring DarkOwl Threat Intelligence Credential Monitoring Dark Web Intelligence
What Does DarkOwl Do Well? DarkOwl is a darknet data platform. They collect content from across the dark web and make it …
Dark Web Monitoring Compromised Credentials Group-IB Threat Intelligence Credential Monitoring
What Does Group-IB Do? Group-IB is a cybersecurity company that sells a suite of products under their Unified Risk …

Digital Risk Protection Dark Web Monitoring Compromised Credentials Threat Intelligence Credential Monitoring
What Does Digital Risk Protection Actually Cover? Vendors use “digital risk protection” loosely. Gartner and Forrester …
Dark Web Monitoring Compromised Credentials Flare Threat Intelligence Credential Monitoring
What Does Flare Do? Flare is a threat exposure management platform. They monitor dark web sources and clear web …

Dark Web Monitoring Compromised Credentials SpyCloud Threat Intelligence Credential Monitoring
What Does SpyCloud Do Well? SpyCloud’s dark web monitoring focuses on extracting stolen credentials from third-party …

Authentication Dark Web Monitoring Credential Monitoring Security Tools
Top 10 Account Takeover Solutions at a Glance Platform Category Best For Breachsense Credential Intelligence Dark web …

Dark Web Monitoring Compromised Credentials DarkOwl Threat Intelligence Credential Monitoring
What Does DarkOwl Do? DarkOwl is a darknet data platform. They collect content from across the dark web and make it …

Dark Web Monitoring Threat Intelligence Credential Monitoring Security Research
What Is a Dark Web Market? When your credentials get stolen, they often end up for sale on a dark web market within …
Data Breach Credential Monitoring
What Is Data Breach Detection? Most companies don’t know they’ve been breached. Not for weeks. Often not even for …

Dark Web Monitoring Threat Intelligence SocRadar Digital Risk Protection Credential Monitoring
What Does SocRadar Do? SocRadar markets itself as an “Extended Threat Intelligence” platform. That’s their branding for …

Dark Web Monitoring ZeroFox Digital Risk Protection Compromised Credentials Credential Monitoring
What Does ZeroFox Do? ZeroFox is a digital risk protection platform that monitors external threats across social media …
Threat Intelligence Recorded Future Dark Web Monitoring Compromised Credentials Credential Monitoring
What Does Recorded Future Do? Recorded Future is an enterprise threat intelligence platform providing broad coverage …

Dark Web Monitoring Compromised Credentials SpyCloud Threat Intelligence Credential Monitoring
What Does SpyCloud Do? SpyCloud is an enterprise-focused platform that detects stolen credentials to prevent account …

Dark Web Monitoring MSP Cybersecurity Tools Credential Monitoring Managed Service Providers
Platform Best For Key Strength Breachsense API-first MSPs Multi-tenant API, infostealer coverage ID Agent Dark Web ID …

Data Breach Detection Dark Web Monitoring Credential Monitoring Cybersecurity Tools Threat Intelligence
What Are Data Breach Detection Tools? Most security tools watch your internal network. Breach detection tools watch …

Data Breach Prevention Credential Monitoring Dark Web Monitoring Cybersecurity
What Is Data Breach Prevention? Most security tools watch for attackers inside your network. By then, it’s often too …

Dark Web Monitoring Threat Intelligence Credential Monitoring
What Is Deep Web Monitoring? Most security discussions focus on the dark web. But threats often appear elsewhere first. …
Dark Web Monitoring Credential Monitoring Data Breach
What Are Leaked Emails? Most security teams think about leaked emails as a consumer problem. Check your personal email …

Credential Monitoring Dark Web Monitoring Data Breach Security Tools
What Are Dark Web Monitoring Tools? Dark web monitoring tools scan criminal sources for exposed passwords linked to your …

Account Takeover Authentication Credential Monitoring
What Is Password Spraying? Account lockout policies exist to stop password guessing. Attackers adapted. Password …
Account Takeover Credential Monitoring Data Breach
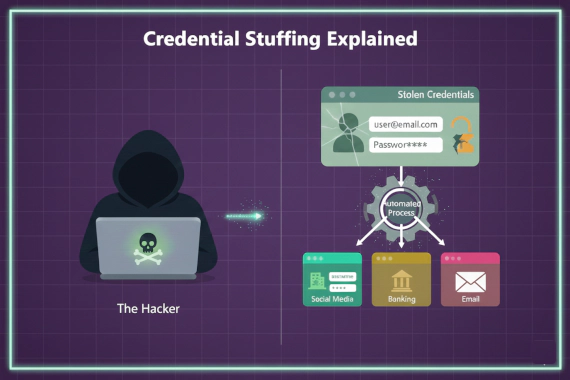
What Is Credential Stuffing? Most people hear “credential stuffing” and think it’s just another brute force attack. It’s …

Credential Monitoring Data Breach Dark Web Monitoring
Where Do Leaked Corporate Credentials Appear? Corporate credentials leak through multiple channels. Security teams need …