March 2026 Ransomware Report: 808 Victims, 65 Groups
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
March 2026 ransomware numbers at a glance March was the busiest month of 2026 so far. Here’s what it means for you. …

Which ransomware groups claimed the most victims in April 2026, which industries got hit hardest, and what shifted from Q1 into the new quarter.
• 772 victims in April, down 4.5% from March’s 808 but still 27% above the 2025 monthly average. Q1 + April totals 2,937 victims, on pace for ~8,800 by year-end.
• Qilin still on top with 103 victims, but their lead narrowed. TheGentlemen jumped to 82 victims, DragonForce broke into the top three with 63. Tracking just Qilin won’t cover you anymore.
• Healthcare returned to the #1 industry spot with 64 victims, up from 47 in March. Manufacturing fell from 76 victims to 50. Technology jumped from 36 to 56.
• The US dropped from 50% of victims to 39% (304 of 772). Canada (28 victims), UK (34), and Germany (37) all rose. The geographic spread keeps widening.
Breachsense tracked 772 companies claimed by ransomware groups in April 2026. That’s slightly below March’s 808 but still well above January and February’s ~680 each.
We compiled this data from ransomware groups’ own leak sites where they publicly list victims. The numbers reflect claimed victims, not confirmed breaches. Some claims are exaggerated or duplicated across groups.
70 distinct ransomware groups were active in April, up from 65 in March. New groups keep appearing.
Here’s what the April 2026 numbers tell us.
After March’s spike, April pulled back slightly. Here’s what changed.
Ransomware leak sites are dark web pages where ransomware operators publish stolen data from victims who refuse to pay. Many groups steal data and threaten to leak it; some also encrypt files. A growing share (ShinyHunters, WorldLeaks, Cl0p) skip encryption entirely and run pure data-extortion operations.
Four months in, the 2026 total is 2,937 victims. That annualizes to roughly 8,800, a 20% increase over 2025’s total of 7,307. The growth trend isn’t slowing.
Qilin still leads, but their lead narrowed. TheGentlemen and DragonForce both moved up.
| Rank | Group | Victims | Change from Mar |
|---|---|---|---|
| 1 | Qilin | 103 | -28 |
| 2 | TheGentlemen | 82 | +18 |
| 3 | DragonForce | 63 | +9 |
| 4 | Akira | 48 | -36 |
| 5 | INC_RANSOM | 41 | -5 |
| 6 | LockBit | 39 | -12 |
| 7 | CoinbaseCartel | 36 | +14 |
| 8 | FulcrumSec | 22 | new |
| 9 | Payload | 20 | +4 |
| 10 | KRYBIT | 20 | new |
The top 10 groups accounted for 474 victims (61.4%). The remaining 60 groups split the other 298. That’s a more diluted distribution than March, where the top 10 took 67.7%.
Qilin posted 103 victims, down from 131 in March. Four months in a row above 100, but the gap to second place shrank from 47 victims in March to 21 in April. Still the most consistent operation in the game, just no longer the runaway leader.
TheGentlemen climbed back to 82 victims after dropping to 64 in March. Their January-to-February jump (41 to 78) wasn’t a fluke. They’re settling in as a reliable top-three group.
DragonForce posted 63 victims, up from 54 in March and 30 in February. They’ve grown every month this year. If the trend holds, they’ll cross Qilin’s volume in the next quarter or two.
Akira dropped to 48 victims from March’s 84. The rebound we saw in March didn’t sustain. Akira’s monthly victim count swings wildly: Jan 71, Feb 39, Mar 84, Apr 48.
LockBit posted 39 victims, down from 51. Still in the top six, still well below their pre-disruption peak. The slow-burn comeback continues.
FulcrumSec and KRYBIT are new to the top ten. FulcrumSec posted 22 victims in their first month tracked, KRYBIT 20.
Sub-top-10 movers worth flagging: ShinyHunters (18), LAMASHTU (17), NightSpire (15), Bashe (15) all posted double-digit counts.
The US share dropped 11 percentage points. The geographic spread keeps widening.
| Rank | Country | Victims | % of Total |
|---|---|---|---|
| 1 | United States | 304 | 39.4% |
| 2 | Germany | 37 | 4.8% |
| 3 | United Kingdom | 34 | 4.4% |
| 4 | Canada | 28 | 3.6% |
| 5 | France | 27 | 3.5% |
| 6 | Italy | 26 | 3.4% |
| 7 | Spain | 21 | 2.7% |
| 8 | Australia | 19 | 2.5% |
| 9 | India | 16 | 2.1% |
| 10 | Thailand | 16 | 2.1% |
The US share fell from 50% in March to 39% in April. Total US victims dropped from 404 to 304, a hundred-victim swing in one month. It’s too early to call this a trend, but it’s the largest single-month drop in US share we’ve tracked this year.
Germany climbed to second with 37 victims, up from 32 in March. Germany has been steadily rising all year.
The UK rebounded to 34 victims from March’s 24. The UK monthly count goes February 44, March 24, April 34. It swings more than most.
Canada jumped to 28 victims, up from 17 in March. That’s the biggest month-over-month increase among the top countries.
France dropped from 36 victims to 27. The February-March surge didn’t continue.
79 countries were hit in total, up from 75 in March. More countries every month.
Healthcare came back to the top. Manufacturing kept declining.
Double extortion ransomware is an attack where criminals steal your data before encrypting it. If you restore from backups and refuse to pay, they threaten to publish the stolen data on leak sites. This makes backups alone an incomplete defense.
| Rank | Industry | Victims | Change from Mar |
|---|---|---|---|
| 1 | Healthcare | 64 | +17 |
| 2 | Technology | 56 | +20 |
| 3 | Manufacturing | 50 | -26 |
| 4 | Legal | 40 | -3 |
| 5 | Consumer Goods | 37 | +9 |
| 6 | Construction | 37 | -16 |
| 7 | IT | 31 | -4 |
| 8 | Education | 30 | +4 |
| 9 | Engineering | 29 | new in top 10 |
| 10 | Finance | 28 | -20 |
Healthcare returned to the #1 spot with 64 victims, up from 47 in March. February’s spike (93) wasn’t a peak. It was the start of an uneven climb. Healthcare’s monthly volume in 2026: 40 → 93 → 47 → 64. Volatile, but staying well above the 2025 average.
Technology jumped to second place with 56, up from 36 in March. Tech companies have been a steady mid-tier target all year. This is their highest month so far.
Manufacturing dropped to third place with 50 victims, down from 76 in March and 94 in February. Manufacturing held the top spot for two months running but is clearly cooling off. Whether attackers are actually moving away from manufacturing or just rotating targets, May will tell us.
Construction fell from 53 victims to 37. The March surge looks like a blip, not a sustained shift.
Finance dropped from 48 victims to 28. Notable because finance was climbing month-over-month through Q1.
Government held at 28 victims, basically flat from March’s 31.
FulcrumSec (22 victims): New to our tracking. 22 victims in their first month is a strong debut, similar to CoinbaseCartel’s 22 in March.
KRYBIT (20 victims): Another new name with a notable first month.
LAMASHTU (17 victims): Already established but climbing.
ShinyHunters (18 victims): Less a traditional ransomware group, more a data-extortion operation. Volume is climbing.
WorldLeaks (13 victims): Steady volume, established group.
The number of active groups grew from 65 to 70. Five months in, the pattern holds: new groups keep appearing while established ones maintain or grow their volume. Consolidation isn’t happening.
| Metric | January | February | March | April | YTD Total |
|---|---|---|---|---|---|
| Total victims | 677 | 680 | 808 | 772 | 2,937 |
| Active groups | 58 | 54 | 65 | 70 | – |
| Countries hit | 60 | 72 | 75 | 79 | – |
| Industries hit | 61 | 63 | 72 | 72 | – |
| Top group | Qilin (107) | Qilin (104) | Qilin (131) | Qilin (103) | Qilin (445) |
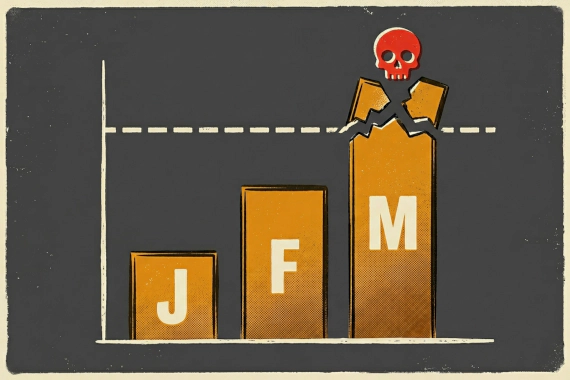
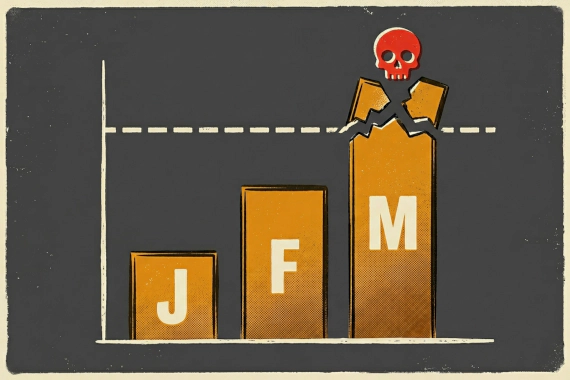
April pulled back from March’s high but stayed well above Q1’s flat baseline of ~680. Every 2026 month so far has run ahead of any month in 2025.
Qilin led the YTD chart with 445 total victims across four months. TheGentlemen is second with 265 victims (41 + 78 + 64 + 82). DragonForce has 207 victims across four months and is growing.
70 active groups in April, up from 58 in January. The ecosystem is fragmenting and growing simultaneously.
April’s numbers don’t show a slowdown. The shape of the threat is just shifting.
Watch the top 3 changing. Qilin still leads, but TheGentlemen and DragonForce have closed the gap. If you’ve been monitoring for Qilin TTPs specifically, broaden the watch list. Three groups can hit at the volume Qilin used to hit alone.
Healthcare and tech took the top two slots. If you’re in those sectors or your vendors are, expect more ransomware attempts and data-extortion campaigns. Healthcare hit 64 victims this month, technology 56. That’s 120 victims in two industries, roughly 15.5% of all April ransomware attacks.
The US share is dropping. That doesn’t mean US companies are safer. It means more groups are casting wider nets. Canada, Germany, UK, and Australia all saw increases. If you have international subsidiaries, your exposure profile is changing.
Check your credential exposure. Most ransomware attacks start with stolen credentials purchased from infostealer logs. There’s a gap between when credentials are stolen and when ransomware deploys. Dark web monitoring catches credentials in that window. With five-plus new groups appearing every month, waiting until something hits your network is too late. You need to see the credentials before they get exploited.
This data reflects publicly claimed victims only. The actual number of attacks is higher because:
When multiple groups claim the same victim, we count it once for the total but list it under each claiming group in the per-group breakdown. Industry and country are based on the company’s primary business and headquarters.
Breachsense tracked 772 companies listed on ransomware leak sites in April 2026, from 70 distinct groups across 79 countries. The actual number of attacks is higher since many victims pay before being publicly listed.
Qilin claimed 103 victims in April 2026, holding the top spot for the fourth straight month but with a much narrower lead. TheGentlemen was second with 82 victims, and DragonForce was third with 63.
The US accounted for 39% of all ransomware victims in April 2026 with 304 claims, down from 50% in March. Germany was second with 37 victims, the UK third with 34, Canada fourth with 28, and France fifth with 27.
Healthcare was the most targeted sector in April 2026 with 64 victims, returning to the top spot after dropping in March. Technology was second with 56 victims and manufacturing third with 50. Legal services and consumer goods posted 40 and 37 victims respectively.
Yes. The four-month total of 2,937 victims puts 2026 on pace for roughly 8,800 by year-end, up 20% from 2025’s total of 7,307. April was below March’s peak but still the third-highest month we’ve tracked.
Most ransomware groups buy stolen credentials from infostealer malware logs rather than breaking in themselves. There’s often a gap of days to weeks between when credentials are stolen and when ransomware gets deployed. Monitoring for leaked credentials can help you catch and reset them before attackers use them.
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
March 2026 ransomware numbers at a glance March was the busiest month of 2026 so far. Here’s what it means for you. …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
February 2026 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. …