March 2026 Ransomware Report: 808 Victims, 65 Groups
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
March 2026 ransomware numbers at a glance March was the busiest month of 2026 so far. Here’s what it means for you. …

Learn which ransomware groups hit the most companies in 2025 and what changed from 2024.
• 7,307 companies were listed on ransomware leak sites in 2025, up 45% from 2024. The pace is accelerating, not plateauing.
• Qilin went from #9 to #1 while LockBit fell from #1 to #13. Tracking last year’s top groups won’t protect you this year.
• Healthcare was hit hardest with 538 victims. Manufacturing grew 71% YoY. If you’re in either sector, you’re a primary target.
• 51.8% of all victims were US companies. If you’re US-based, you face disproportionate risk.
• 138 groups were active in 2025, up 41% from 2024. The ecosystem is fragmenting. Smaller operations now account for nearly half of all attacks.
Breachsense tracked 7,307 companies claimed by ransomware groups in 2025. That’s a 45% increase over the 5,028 victims we tracked in 2024.
This data comes from Breachsense’s daily indexing of ransomware leak sites, where groups publicly list victims who refuse to pay. These are claimed victims, not confirmed breaches. Some claims are exaggerated or duplicated across groups.
The numbers tell a clear story: more groups, more victims. And the operations running the most attacks aren’t the same ones from 2024.
Here’s what 2025 looked like.
You’ll see “leak site” throughout this report. Here’s what that means. Breachsense monitors these sites daily.
Ransomware leak sites are dark web pages where ransomware operators publish stolen data from victims who refuse to pay. Most modern ransomware groups use double extortion: they steal your data before encrypting it, then threaten to leak it publicly. Breachsense indexes these sites daily.
Here’s how 2025 compared to 2024:
| Metric | 2024 | 2025 | Change |
|---|---|---|---|
| Total victims | 5,028 | 7,307 | +45% |
| Active groups | 98 | 138 | +41% |
| Countries affected | 120+ | 120+ | — |
| Industries affected | 75+ | 75 | — |
| Monthly average | 419 | 609 | +45% |
| Peak month | December (594) | February (878) | +48% |
The 45% jump wasn’t a gradual increase. Attacks surged in February 2025, dipped in May, then climbed steadily from September through December.
Attack volume swung widely throughout the year. February 2025 was the deadliest month with 878 victims, likely driven by CL0P’s mass exploitation campaigns. May was the quietest at 363.
| Month | 2024 | 2025 | YoY Change |
|---|---|---|---|
| January | 278 | 535 | +92% |
| February | 357 | 878 | +146% |
| March | 325 | 743 | +129% |
| April | 388 | 511 | +32% |
| May | 547 | 363 | -34% |
| June | 305 | 440 | +44% |
| July | 424 | 509 | +20% |
| August | 399 | 487 | +22% |
| September | 427 | 583 | +37% |
| October | 470 | 761 | +62% |
| November | 490 | 679 | +39% |
| December | 594 | 777 | +31% |
Two patterns stand out. First, 2025 started with a surge. January through March averaged 719 victims per month, nearly double the same period in 2024. Second, the final quarter of 2025 averaged 739 victims per month, the highest sustained rate we’ve seen.
May 2025’s drop to 363 victims is an outlier. It’s also the only month where 2025 fell below 2024. This often happens after major law enforcement operations or when dominant groups go temporarily quiet between campaigns.
The top of the leaderboard changed completely.
| 2025 Rank | Group | 2025 Victims | 2024 Rank | 2024 Victims | Change |
|---|---|---|---|---|---|
| 1 | Qilin | 958 | 9 | 167 | +474% |
| 2 | Akira | 735 | 4 | 255 | +188% |
| 3 | CL0P | 469 | 35 | 31 | +1,413% |
| 4 | Play | 376 | 3 | 349 | +8% |
| 5 | INC_RANSOM | 365 | 11 | 150 | +143% |
| 6 | SafePay | 361 | 30 | 38 | +850% |
| 7 | Lynx | 224 | 21 | 66 | +239% |
| 8 | Ransomhub | 221 | 2 | 508 | -56% |
| 9 | DragonForce | 214 | 16 | 88 | +143% |
| 10 | Sinobi | 170 | — | — | New |
The top 10 groups claimed 4,093 victims, about 56% of the total. That’s concentrated, but less than you’d expect. The remaining 128 groups split the other 3,214 victims.
Qilin’s jump from 167 victims in 2024 to 958 in 2025 is the year’s biggest story. That’s a 474% increase. They went from a mid-tier operation to claiming more victims than any other group by a wide margin.
Qilin operates a ransomware-as-a-service platform where affiliates (the people who actually break in) use Qilin’s tools and infrastructure. Their growth suggests they attracted affiliates leaving other operations, particularly LockBit and Ransomhub.
LockBit was the most feared ransomware operation for years. In 2024, they claimed 513 victims and ranked #1. In 2025, they dropped to 113 victims and ranked #13.
Operation Cronos in February 2024 seized LockBit’s infrastructure and unmasked its alleged leader. That shattered affiliate trust. Most moved to Qilin and Akira, operations that weren’t compromised.
CL0P had only 31 victims in 2024 after their massive MOVEit campaign in 2023. They came back in 2025 with 469 victims, a 1,413% increase. CL0P’s pattern is distinctive. They don’t break into companies one at a time. They find a zero-day vulnerability in widely used software, exploit it across hundreds of organizations simultaneously, then go quiet until the next campaign.
Their February 2025 spike (contributing to the 878-victim month) follows this pattern exactly.
Several groups that barely existed in 2024 hit hard in 2025:
Ransomhub was the #2 group in 2024 with 508 victims. They dropped to 221 in 2025, a 56% decline. This pattern repeats across ransomware. Groups that attract too much attention eventually get disrupted and lose affiliates.
Healthcare topped the list for the first time in our tracking, overtaking construction which led in 2024.
| 2025 Rank | Industry | 2025 Victims | 2024 Victims | YoY Change |
|---|---|---|---|---|
| 1 | Healthcare | 538 | 386 | +39% |
| 2 | Manufacturing | 473 | 277 | +71% |
| 3 | Construction | 418 | 439 | -5% |
| 4 | Technology | 392 | 17 | +2,206% |
| 5 | Legal | 350 | 222 | +58% |
| 6 | Consumer Goods | 335 | 175 | +91% |
| 7 | Finance | 316 | 211 | +50% |
| 8 | Education | 282 | 223 | +26% |
| 9 | Government | 277 | 201 | +38% |
| 10 | Food | 222 | 126 | +76% |
| 11 | Real Estate | 220 | 121 | +82% |
| 12 | Automotive | 189 | 141 | +34% |
| 13 | IT | 187 | 189 | -1% |
| 14 | Logistics | 181 | 102 | +77% |
| 15 | Engineering | 170 | 16 | +963% |
75 industries were affected in total. No sector was spared.
Note: Some industry categories were reclassified between 2024 and 2025 (e.g., “Industrial” and “Software” in 2024 were recategorized), which affects some YoY comparisons.
Healthcare organizations accounted for 7.4% of all ransomware victims in 2025. That’s more than one healthcare organization hit every single day.
Healthcare is a prime target for double extortion because patient data is sensitive and operations can’t afford downtime. The Change Healthcare breach in early 2024 showed how a single attack can disrupt healthcare payments nationwide. 2025’s numbers show the sector hasn’t gotten better at defending itself.
Manufacturing jumped from 277 victims in 2024 to 473 in 2025. That’s the largest absolute increase among the top industries. Manufacturers run legacy systems and have complex supply chains. Production downtime is expensive, so they face enormous pressure to pay quickly.
Construction was the only top-5 industry to see a year-over-year decline. It led all industries in 2024 with 439 victims and dropped slightly to 418. The sector remains heavily targeted but other industries grew faster around it.
Law firms hold privileged client communications and merger documents. The threat isn’t just encryption. It’s having confidential client files published on a leak site. That makes double extortion especially effective against legal targets.
Government agencies accounted for 277 victims, up from 201 in 2024. Local governments and school districts are frequent targets because they run outdated systems with limited security budgets. CISA’s StopRansomware initiative tracks these attacks and publishes advisories for affected sectors.
The United States was the primary target, accounting for more than half of all victims. Every top-10 country saw an increase.
| Rank | Country | 2025 Victims | 2024 Victims | YoY Change |
|---|---|---|---|---|
| 1 | United States | 3,784 | 2,595 | +46% |
| 2 | Canada | 386 | 251 | +54% |
| 3 | Germany | 274 | 153 | +79% |
| 4 | United Kingdom | 255 | 203 | +26% |
| 5 | France | 169 | 109 | +55% |
| 6 | Italy | 161 | 129 | +25% |
| 7 | Spain | 144 | 104 | +38% |
| 8 | Brazil | 132 | 121 | +9% |
| 9 | India | 128 | 108 | +19% |
| 10 | Australia | 120 | 103 | +17% |
120+ countries were affected. The top 10 accounted for 75.7% of all victims.
3,784 US companies were hit in 2025, up 46% from 2,595 in 2024. That’s more than the next nine countries combined. Several factors drive this:
Europe collectively saw over 1,200 victims. Germany (274) and UK (255) were the hardest hit. France and Italy each saw over 160. Spain had 144. European companies face both international groups and region-specific operations.
Asia-Pacific accounted for roughly 700 victims. India (128) and Australia (120) topped the regional list. Southeast Asian countries collectively accounted for over 250 victims.
Latin America saw 500+ victims. Brazil (132) and Mexico (75) were the most targeted. Ransomware groups have expanded into the region as competition for US and European victims intensifies.
Middle East had 200+ victims. Israel (66) and the UAE (62) were hit hardest.
The biggest trend in 2025 wasn’t any single group or attack. It was the continued fragmentation of the ransomware ecosystem.
Ransomware-as-a-service (RaaS) is a business model where ransomware developers rent their tools to affiliates who carry out the actual attacks. You don’t need to build your own malware. You sign up, get access to the encryption tools and leak site, then split the ransom with the developer.
138 groups claimed victims in 2025, up from 98 in 2024. That’s 41% more operations in a single year. In 2024, the top 5 groups (LockBit, Ransomhub, Play, Akira, Hunters) accounted for 1,825 victims, about 36% of the total. In 2025, the top 5 (Qilin, Akira, CL0P, Play, INC_RANSOM) accounted for 2,903 victims, about 40%.
The top is slightly more concentrated, but below the top 10, dozens of small operations each claimed between 10 and 50 victims. These smaller groups are often harder to track and less likely to be targeted by law enforcement.
This fragmentation happens because ransomware-as-a-service makes it easy to launch new operations. When law enforcement disrupts a major group, its affiliates don’t stop. They move to existing alternatives or start their own operations. The barrier to entry keeps dropping.
Most ransomware groups don’t break in through zero-days or advanced exploits. They buy access. The typical attack chain looks like this:
There’s a gap between when credentials get stolen and when ransomware gets deployed. That gap is typically days to weeks. Dark web monitoring can detect stolen credentials in that window. That gives you time to reset passwords and revoke sessions before attackers use them.
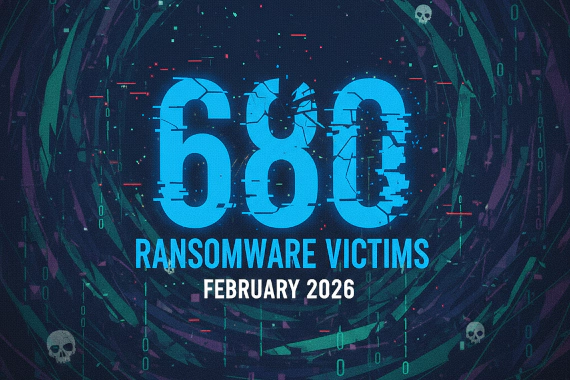
If 2025’s trajectory continues, 2026 will be worse. January 2026 already saw 677 victims across 58 groups, an 11% increase over the 2025 monthly average.
The groups driving the most volume in 2025 are still active. Qilin and Akira show no signs of slowing down. New operations continue to appear weekly.
For security teams, the data points to three priorities:
Monitor for stolen credentials. Most ransomware attacks start with compromised credentials bought from infostealer logs. If you can detect and reset stolen credentials before attackers use them, you close the most common entry point. Compromised credential monitoring catches this.
Don’t just track the big names. With 138 active groups, the threat isn’t limited to the top 10. Smaller operations are responsible for nearly half of all attacks.
Assume you’re a target. 75 industries were hit across 120+ countries. No sector or geography is immune.
This report is based on Breachsense’s daily indexing of ransomware leak sites throughout 2025. We monitor these sites directly and catalog every victim listing.
The numbers reflect publicly claimed victims only. The actual attack count is higher because:
When multiple groups claim the same victim, we count it once. Industry and country classifications are based on each company’s primary business and headquarters location.
Year-over-year comparisons use the same methodology applied to 2024 data.
For real-time ransomware and credential monitoring, book a demo.
Breachsense tracked over 7,300 companies listed on ransomware leak sites in 2025. The actual number is higher since many victims pay before being listed. Monthly averages rose from 419 per month in 2024 to 609 in 2025.
Qilin claimed 958 victims in 2025, making it the most active group by a wide margin. Akira was second with 735 and CL0P third with 469. Qilin jumped from #9 in 2024 to #1 in 2025.
Healthcare was the most targeted industry in 2025 with 538 victims. Manufacturing was second with 473 and construction third with 418. These top five industries accounted for 30% of all victims.
US companies accounted for 51.8% of all ransomware victims in 2025 (3,784 companies). Canada was second with 386 victims (5.3%) and Germany third with 274 (3.8%). Over 120 countries were affected.
138 distinct ransomware groups claimed victims in 2025, up from 98 in 2024. The top 10 accounted for about 56% of all victims. Newer groups like SafePay and Sinobi appeared for the first time and immediately cracked the top 10.
Yes. Victims jumped nearly 50% year over year. The number of active groups grew 41%. Monthly attack rates accelerated through the year, with Q4 2025 averaging 739 victims per month compared to 535 in January.
LockBit dropped from 513 victims (#1 in 2024) to 113 victims (#13 in 2025), a 78% decline. Operation Cronos disrupted the group’s infrastructure in February 2024. They’re still around but much smaller. Most affiliates moved to Qilin and Akira.
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
March 2026 ransomware numbers at a glance March was the busiest month of 2026 so far. Here’s what it means for you. …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
February 2026 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. …