8 Damaging Consequences of a Data Breach Explained.
How Much Does a Data Breach Cost? The financial consequences of a data breach go far beyond the initial incident …

Learn how account takeover fraud works and how to spot compromised credentials early.
• Most ATO attacks start with credentials stolen by infostealer malware or exposed in data breaches. You don’t need to be breached directly for your credentials to end up on the dark web.
• Monitoring the dark web for your organization’s leaked passwords is the most effective defense. When you find exposed credentials early, you can force resets before they’re exploited.
• The 2025 Verizon DBIR found that 54% of ransomware victims had credentials previously exposed in stealer logs. Credential theft and ransomware are directly connected.
• The average credential-based breach costs $4.67 million and takes 246 days to identify and contain. How fast you detect exposed credentials decides whether it’s a password reset or a full incident response.
ATO fraud volume grew 141% between 2021 and 2025, according to Sift. It’s one of the fastest-growing threats security teams face.
Most account takeover attacks start with credentials that were already stolen from data breaches or infostealer malware. Attackers buy them on dark web marketplaces.
Once attackers have valid credentials, they bypass most traditional defenses. There’s no malware to detect and no exploit to flag.
This guide breaks down how ATO fraud works, what it looks like in practice, and how to detect it before attackers cause real damage.
Account takeover fraud starts with a stolen password and ends with an attacker inside your systems.
Account takeover fraud (also called ATO fraud) is a type of cyber attack where an attacker gains unauthorized access to a legitimate user’s account using compromised login details. Unlike traditional identity theft, which involves creating new fraudulent accounts, ATO fraud exploits existing accounts that already have access to data and funds.
The account takeover meaning is straightforward: someone who isn’t the account owner takes control of it. But the consequences are anything but simple.
ATO fraud differs from other fraud types in important ways. Credit card fraud involves stealing payment details to make unauthorized purchases. Identity theft involves using personal information to open new accounts. Account takeover attacks skip both steps. Attackers use valid credentials to log in as the real user, which makes these attacks harder to detect and more damaging when they succeed.
Global ATO losses reached an estimated $17 billion in 2025, according to Sift’s Digital Trust Index. ATO fraud volume grew 141% between 2021 and 2025, driven largely by infostealer malware and the growing supply of compromised logins on underground markets.
The Verizon 2025 DBIR found that stolen credentials were the top initial access vector, involved in 22% of all breaches. In web application attacks specifically, 88% involved compromised passwords. Attackers use credentials because they work.
Every account takeover attack follows the same basic chain: steal credentials, test them, get in, then exploit the access.
Attackers first need valid credentials. They get them from several sources:
Infostealer malware is the primary source of exploitable credentials today. When someone downloads a fake software installer or clicks a malicious link, the infostealer harvests every saved password from their browser, along with session cookies and autofill data. This data hits criminal marketplaces within hours.
Stealer logs are data packages created by infostealer malware containing a victim’s harvested credentials and browser cookies. These logs also include autofill data and system information. They’re sold on underground markets and Telegram channels, giving attackers ready-to-use credentials for account takeover attacks.
The 2025 Verizon DBIR found that 54% of ransomware victims had credentials previously exposed in infostealer logs. That’s a direct line from credential theft to ransomware.
Third-party data breaches expose user databases containing millions of credentials. These get aggregated into combo lists that attackers test against other sites. Password reuse turns one breach into access across dozens of services.
Credential stuffing automates this at scale. Attackers use bots to test leaked username-password pairs against multiple sites simultaneously, exploiting password reuse across personal and corporate accounts.
Phishing remains effective for targeted attacks. Modern phishing kits create convincing fake login pages that capture credentials in real time. Some kits can even intercept MFA codes before they expire.
Attackers don’t try credentials one at a time. They use automated tools to test thousands of credential pairs against target login pages. Botnets distribute these attempts across thousands of IP addresses to avoid rate limiting.
Once a valid credential pair works, the attacker logs in. Because they’re using legitimate credentials, this looks identical to a normal user session. There’s no malware signature and no exploit to flag.
With infostealers, attackers often skip authentication entirely. Stolen session cookies let them hijack active sessions without needing the password or MFA code.
What happens next depends on the attacker’s goals. They might change account settings to lock out the real user. They might steal data or commit financial fraud. Some use the compromised account as a launchpad to move deeper into the network.
ATO fraud hits different industries in different ways. Here are the most common patterns security teams encounter.
Business email compromise is one of the most financially damaging forms of ATO fraud. An attacker takes over an executive’s email account and uses it to redirect wire transfers or impersonate leadership to other employees.
The FBI’s IC3 reported $2.77 billion in BEC losses in 2024 alone, with cumulative losses exceeding $17.1 billion over the past decade. BEC works because the emails come from a real, trusted account. There’s nothing to flag as suspicious.
A typical BEC attack starts when an attacker buys an executive’s credentials from a criminal marketplace. They log in, study email patterns for a few days, then send a convincing payment redirect request to the finance team. The email comes from the real CEO’s account and references a real vendor.
Attackers target banking and payment accounts for direct monetary gain. They log in with compromised credentials, change notification settings to hide their activity, then drain accounts or make fraudulent purchases.
Financial ATO often starts with credentials from a completely unrelated breach. An employee reuses their banking password on a forum that gets hacked. The attacker buys the combo list and tests it against banking sites.
Financial institutions are prime targets because the payoff is immediate. Attackers can transfer funds or open new credit lines before the account holder notices anything wrong. Many financial ATO attacks happen outside business hours when fraud teams have slower response times.
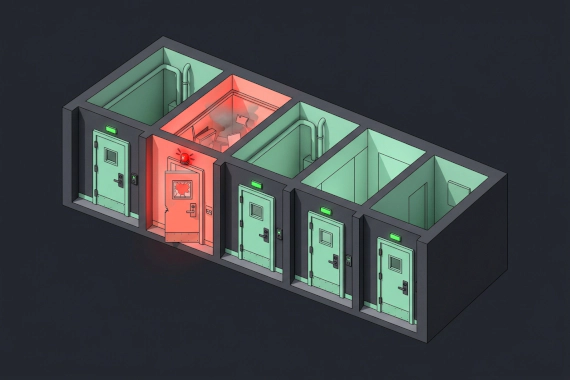
Corporate SaaS accounts are high-value targets. A compromised Slack or Microsoft 365 account gives attackers access to internal communications and shared documents. Connected integrations expand the blast radius further.
SaaS account takeover is especially dangerous because of single sign-on (SSO). One compromised identity provider account can spread into access across every connected application. Attackers who take over an admin account in your identity platform effectively own your entire SaaS stack.
Cloud infrastructure accounts carry even higher stakes. A compromised AWS or Azure admin account can give attackers the ability to exfiltrate data or deploy cryptominers. Cloud ATO attacks often go undetected because the attacker’s actions look like normal administrative activity.
The best time to catch an ATO attack is before the attacker logs in. The second best time is the moment they do.
The most effective account takeover detection starts outside your network. Your organization’s credentials are circulating on criminal forums and in stealer logs right now. The question is whether you find them first.
Compromised credential monitoring scans criminal marketplaces and infostealer channels for your organization’s exposed passwords. When it finds leaked credentials, your team can force resets before anyone exploits them. This turns a potential ATO attack into a routine password change.
Dark web monitoring should run continuously, not as periodic scans. Credentials can appear on underground markets and be exploited within hours. Daily or weekly scans leave too large a window.
When prevention fails, detection signals help you catch attacks in progress:
Impossible travel. A user logs in from New York, then from Singapore 30 minutes later. Legitimate users don’t teleport. Impossible travel patterns are one of the strongest indicators of credential compromise.
Failed authentication spikes. Multiple failed login attempts followed by a successful login often indicate credential stuffing or password spraying. The failures represent attackers testing credentials. The success means they found a match.
Unexpected MFA requests. When users receive MFA prompts they didn’t initiate, someone is testing their credentials. MFA fatigue attacks bombard users with approval requests, hoping they’ll eventually click “yes” to make it stop.
Account setting changes. Attackers often change recovery emails or notification settings after gaining access. Alert on all account setting changes and require re-authentication before allowing them.
Unusual access patterns. A finance employee suddenly downloading engineering documents. A dormant account becoming active after months. Access patterns that deviate from established baselines deserve investigation.
Session anomalies. Sessions that suddenly switch IP addresses or user agents mid-session suggest session token theft. If a user’s session jumps from a Windows desktop in Chicago to a Linux machine in Eastern Europe, the session has been hijacked.
Credential monitoring and behavioral detection work best together. Credential monitoring catches attacks at the source. Behavioral detection catches the attacks that get through. Neither approach alone covers every ATO scenario.
For a deeper dive into stopping these attacks, see our guide on account takeover prevention. For a comparison of tools, check our account takeover solutions guide.
ATO fraud costs you far more than the immediate financial loss. Fines and lost customers pile up fast. Operational downtime makes it worse.
IBM’s 2025 Cost of a Data Breach Report puts the average cost of a credential-based breach at $4.67 million. These breaches also take an average of 246 days to identify and contain, giving attackers months of undetected access.
That’s just the breach cost. You’re also dealing with fraudulent transactions and stolen funds. BEC fraud alone cost victims $2.77 billion in 2024. Financial account takeover can drain accounts before fraud teams even notice.
Data protection regulations treat credential-based breaches the same as any other breach. GDPR and HIPAA both require notification when personal data is compromised through account takeover. PCI DSS adds requirements for payment data.
Regulatory fines add up fast. GDPR penalties can reach 4% of global annual revenue. Healthcare organizations face HIPAA penalties for compromised provider accounts that expose patient records. Financial institutions deal with PCI DSS compliance failures when payment data is accessed through compromised passwords.
When customers learn their accounts were taken over, trust drops immediately. They question whether you can protect their data. Some leave and don’t come back.
The reputational damage extends beyond the customers directly affected. News coverage of account takeover incidents damages brand perception across your entire customer base. Rebuilding trust after a publicized ATO incident takes years.
When business accounts are compromised, operations stall. IT teams spend days investigating the scope of compromise and resetting credentials. Employees lose access to critical systems during remediation. Business processes that depend on compromised accounts stop until the investigation is complete.
The operational cost often exceeds the direct financial loss, especially when attackers gain access to systems that control manufacturing or customer-facing services.
After an ATO incident, you’ll typically invest heavily in remediation. This includes forensic investigation and credential resets across the organization. Security tool upgrades and employee retraining follow. Insurance premiums increase. Compliance audits become more frequent.
When you add up investigation and remediation, a single ATO incident can cost several times the initial financial loss. Regulatory response piles on even more.
Account takeover fraud is growing because the supply of exploitable credentials keeps expanding. Infostealers harvest passwords from infected devices daily. Data breaches expose millions of credentials at once. Underground markets make it easy for any attacker to buy valid logins.
The organizations that avoid becoming ATO statistics share one trait: they find leaked passwords early. That means continuous monitoring of dark web sources and stealer logs.
Want to know if your organization’s credentials are already exposed? Check your exposure now.
Account takeover fraud (ATO fraud) is a form of identity theft where an attacker gains unauthorized access to a victim’s online account using stolen credentials. Once inside, the attacker can steal data or commit financial fraud. ATO differs from traditional identity theft because it targets existing accounts rather than creating new ones.
ATO fraud is one of the fastest-growing cyber threats. Global losses reached an estimated $17 billion in 2025, according to Sift. The Verizon 2025 DBIR found that compromised passwords were the #1 initial access vector, involved in 22% of all breaches.
Identity theft involves stealing personal information to create new fraudulent accounts in the victim’s name. Account takeover targets existing accounts using stolen login credentials. ATO fraud is faster to execute because attackers skip account creation and go straight to exploiting an account that already has access and funds.
Attackers get credentials from infostealer malware that harvests saved passwords from browsers. Third-party data breaches also expose user databases. Credential stuffing tests leaked passwords across multiple sites. Phishing attacks trick users into entering credentials on fake login pages.
Financial services and e-commerce are the most targeted industries. Financial accounts offer direct monetary gain. E-commerce accounts store payment methods. SaaS platforms are also growing targets because compromised accounts give access to sensitive business data.
The most effective detection method is dark web monitoring that identifies your organization’s exposed credentials before they’re exploited. Combine this with behavioral signals like impossible travel patterns and failed authentication spikes to catch attacks in progress.
How Much Does a Data Breach Cost? The financial consequences of a data breach go far beyond the initial incident …
What Is Data Breach Mitigation? You can’t prevent every breach. But you can control how much damage one causes. Data …