What is Data Leak Monitoring?
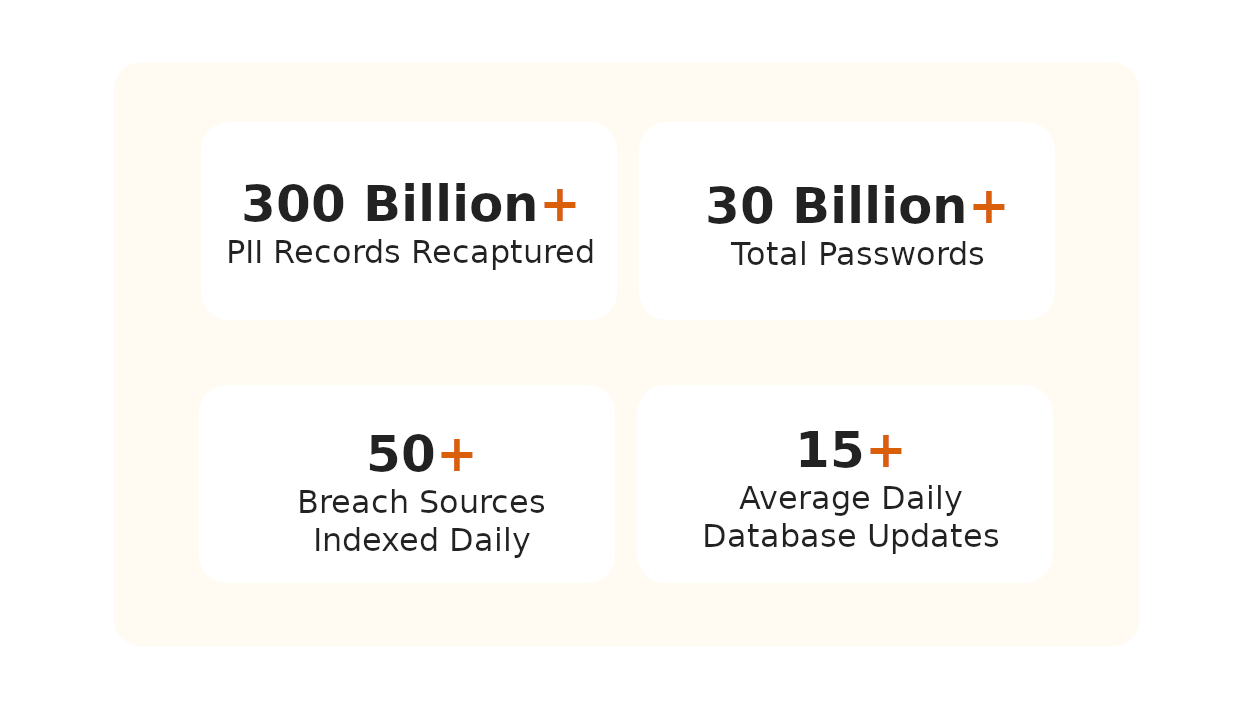
Breachsense tracks hacker forums, Telegram channels, ransomware leak sites, and infostealer logs. We crack hashed passwords to plaintext so you know exactly what’s exposed. You can search by email, domain, or company name and get results across all your monitored assets.
The average company takes 204 days to discover a breach. With leak monitoring, you’ll know within minutes. According to IBM’s 2025 Cost of a Data Breach Report, breaches caught early cost about $1.1 million less than those found late.

Why do you need data leak monitoring?
Stop Credential Theft
Detect Leaks in Real-Time
Reduce Breach Costs
Data Leak Monitoring Trusted by Security Teams Worldwide
Our team uses Breachsense data to gain initial access during pen testing and red team engagements. The API is simple to use and the support is always helpful and responds quickly.
Our Security Colony platform relies on Breachsense data as part of our dark web monitoring service. The data is continuously updated and high quality. Highly recommend!
We rely on Breachsense for a lot of data. Their frequent database updates, constant availability, and handling of big and small breaches alike means we are always covered.
How Does Breachsense Detect Data Leaks?
Add Your Domains & Assets
We Scan Dark Web Sources
Get Instant Leak Alerts
Reset Credentials Fast
Frequently Asked Questions
Data leak monitoring scans the dark web for your exposed credentials, session tokens, and internal documents. It tracks criminal marketplaces, hacker forums, and paste sites for your data. When something appears, you get an alert so you can reset passwords and revoke access before attackers exploit it.
You add your domains and assets to the platform. Breachsense then scans IRC and Telegram channels, private cybercrime communities, and ransomware leak sites for matches. It monitors for employee credentials, C-level executive accounts, remote access credentials (SSH, RDP, FTP), and internal documents. When your data appears, you get an alert with details on what was exposed.
Breachsense monitors hacker forums, criminal marketplaces, Telegram channels, ransomware leak sites, paste sites, and infostealer logs. We also index leaked files from ransomware attacks so you can search for your company name or employee names in vendor breach dumps. Hashed passwords are cracked to plaintext so you know exactly what’s at risk.
Breachsense detects leaked data within minutes of it appearing on monitored sources. The average company takes 204 days to discover a breach without monitoring. According to IBM’s 2025 Cost of a Data Breach Report, breaches caught early cost about $1.1 million less than those found late. Faster detection means less time for attackers to exploit your data.
No. A data leak is an unauthorized release of confidential data, often accidental. Leaks happen through misconfigured databases, human error, or insider actions. A data breach involves deliberate unauthorized access where attackers compromise systems to steal information. Both expose your data, but the cause is different. You need monitoring for both to stay protected.
Reset the compromised passwords immediately. If session tokens were leaked, revoke them so attackers can’t bypass MFA. Check what else was exposed — internal documents, customer records, or access credentials. Notify affected parties if required. Then investigate how the leak happened. Was it a vendor breach? A misconfigured database? An employee reusing passwords? The answer tells you what to fix.
Essential Data Leak Prevention Resources
Guides and tools for data leak detection and prevention
Data Breach Monitoring
Continuous monitoring for breaches affecting your organization. Get real-time alerts when your data appears in third-party breaches or dark web leaks.
Learn MoreCompromised Credential Monitoring
Monitor for leaked employee and customer passwords across the dark web. Reset credentials before attackers exploit them in stuffing attacks.
Learn MoreDark Web Monitoring
Track criminal marketplaces and hacker forums where leaked data is sold. Detect exposed credentials and company data before attackers use it.
Learn MoreCheck Your Exposure
Free scanner to check if your organization’s credentials are on the dark web. See what leaks have exposed your data instantly.
Learn MoreData Leak Guide
How data leaks happen, common causes, and steps to protect your organization from exposure.
Learn MoreData Leak Prevention
Strategies to prevent data leaks before they happen. Implement security controls to stop accidental and intentional data exposure.
Learn MoreData Leak Detection Software
Compare the best data leak detection tools and software. Features, capabilities, and implementation guidance for security teams.
Learn MoreCredential Stuffing Attacks
Learn how attackers use leaked credentials in automated stuffing attacks. Understand the methodology and how to defend against it.
Learn MoreData Breach Mitigation
Immediate steps to take after discovering a data leak or breach. Minimize damage and prevent further exposure.
Learn More