External Attack Surface Management
Attack Surface Management EASM
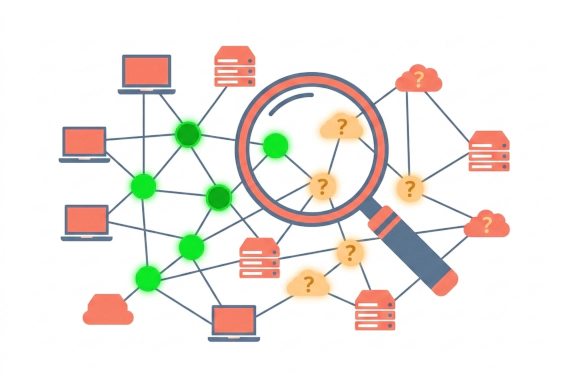
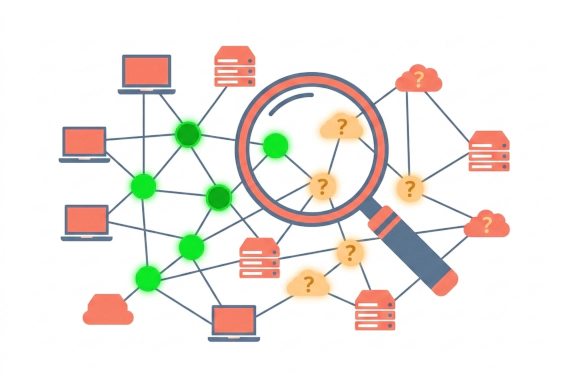
What Are External Attack Surface Management Tools? External attack surface management (EASM) tools continuously discover …

Learn exactly what dark web sources Breachsense monitors and where our coverage has gaps.
• We monitor dark web marketplaces and hacker forums. We also track ransomware leak sites and infostealer channels. This page shows you exactly which sources we cover so you can assess gaps
• 343+ billion compromised credentials indexed. Hashed passwords are cracked to plaintext so alerts are actionable, not just informational
• Alerts fire via webhook or API the moment your data appears. Speed matters because session tokens expire and credentials get exploited fast
• We only index publicly available data. Knowing what we don’t cover is just as important for your risk model
• The breach tracker shows who got hit. The platform shows what leaked. This page covers the platform side
Most dark web monitoring vendors don’t explain where their data comes from. You’re left guessing whether alerts are based on fresh intelligence or recycled combo lists.
This page explains what Breachsense monitors and how alerts work. It also covers where we have blind spots.
If you’re evaluating vendors or need to document your intelligence sources for compliance, this is for you.
We cover what sources we monitor, how alerts work, what our limits are, and how this connects to the breach tracker.
Your credentials could be for sale right now. You’d never know unless you’re actively watching the places where stolen data surfaces. With 60% of breaches involving stolen credentials or a human element, monitoring matters.
Dark web monitoring scans criminal marketplaces and forums for your stolen data. It alerts you when credentials or sensitive files tied to your company appear, so you can reset passwords and lock down accounts before attackers use them.
Here’s what we cover and why each source matters. For definitions of the terms used on this page, see our definitions and terminology reference.
Tor hidden services and .onion marketplaces are where criminals sell credentials and personal data. Our crawlers watch active darknet markets where this data changes hands daily.
Both public and private hacker forums are covered. Attackers discuss targets and post leaked data on these forums. Many breaches surface here before hitting mainstream news.
Over 100 ransomware groups and their leak sites are tracked continuously. When a gang posts a new victim, our monitoring picks it up fast. Browse the full list of tracked groups on the ransomware gangs page. For details on how incidents get verified, see how the breach tracker works.
Logs from RedLine, Vidar, LummaC2, and other credential-stealing malware families get indexed as they appear. Stealer logs contain saved passwords extracted from infected devices, plus active session tokens that bypass MFA. This source is growing faster than any other. Learn more about our infostealer channel monitoring.
Criminal groups use Telegram and hacker forums to distribute stealer logs and sell access. These channels often carry early breach signals before data hits forums.
Paste sites like Pastebin are common drop points for leaked credentials and data samples. Our crawlers check these around the clock.
Complete breach datasets get indexed as they become available, both historical and new. The result is a searchable database of billions of compromised credentials.
Misconfigured Elasticsearch and MongoDB servers leak sensitive data. We catch these exposed databases and index the data before criminals find it.
CT logs show every SSL certificate issued publicly. We watch for certificates issued to suspicious lookalike domains, which helps catch phishing domains impersonating your brand before they’re used in attacks.
Some leaks happen in plain sight. Publicly accessible sources where data surfaces outside the dark web are also covered.
Most enterprise teams don’t try to monitor criminal sources themselves, and for good reason.
Malware risk. Criminal forums and marketplaces are full of malicious downloads. One wrong click and your analyst’s machine is infected. You need isolated infrastructure and strict OpSec just to browse safely.
Getting access. Many forums require vetting or vouching from existing members. Building and maintaining those personas takes months. Lose one and you start over.
Keeping up with new sources. Forums go dark and marketplaces rebrand constantly. New Telegram channels replace old ones. Staying on top of which sources matter right now is a full-time job.
Processing volume. Even if you get access, you’re looking at terabytes of raw data. Stealer logs alone generate millions of records per week. You need pipeline infrastructure to deduplicate records and crack hashes before you can even match against your assets.
This is why most teams use a vendor for collection and focus their own resources on response. For a side-by-side comparison of manual monitoring, threat intel feeds, and automated platforms, see dark web monitoring approaches explained.
You should know what falls outside our coverage.
This is what you can actually search for and get alerts on.
Emails and passwords from data breaches and stealer logs. Hashed passwords get cracked to plaintext so you know exactly what’s exposed. The database holds over 343 billion compromised credentials.
Active authentication tokens extracted from infostealer logs. Attackers use these to bypass passwords and MFA entirely. These alerts are time-sensitive because tokens expire.
Full stealer log entries showing which device was infected and which credentials were extracted. Each entry ties back to a specific malware family and infection timestamp.
Every time a ransomware gang posts a new victim, the announcement gets captured and indexed. You can monitor for your own company or for vendors appearing on leak sites.
Infostealer logs are data packages captured by credential-stealing malware (like RedLine or Vidar) from infected devices. Each log contains saved passwords and session tokens from the victim’s machine. Attackers sell these logs in bulk on dark web channels.
Stolen files published by ransomware groups get indexed. You can search their contents for your company name or employee names to check if your data appears in a vendor’s breach dump.
Homoglyph and typosquatting attacks targeting your brand are detected automatically through CT log monitoring and domain scanning.
Attack surface mapping discovers all subdomains tied to your assets. Forgotten or shadow IT infrastructure gets flagged before attackers find it.
Here’s what happens between a credential appearing on the dark web and you getting an alert.
Continuous collection. Our crawlers monitor all source types 24/7. When new data appears on a marketplace or forum, it gets collected and processed.
Asset matching. You register the domains, emails, IPs, or other assets you want to watch. Every new piece of indexed data gets checked against them.
Real-time notification. When a match is found, an alert fires immediately. You choose the delivery method: webhook or email.
What triggers alerts:
Alerts include context: the source and when it was detected. You can push alerts directly to your SIEM through the Breachsense API.
Every monitoring platform has blind spots. Here are ours.
We only index publicly available data. We don’t buy stolen data from criminals or pay for access to private dumps. If data hasn’t been posted to a source we monitor, we won’t have it.
There’s a gap between breach and detection. When a company gets breached, it can take weeks or months before the stolen data surfaces on the dark web. Companies take an average of 241 days to identify and contain a breach (IBM’s 2025 Cost of Data Breach Report). This delay is most common with third-party breaches where data changes hands privately before going public.
Password cracking depends on hash strength. We crack hashed passwords to plaintext, but success depends on the hash algorithm and whether the breach included salt values. Strong hashing (e.g. bcrypt or argon2id) makes cracking slower.
New dark web sites appear constantly. We add new sources as they become active, but coverage isn’t exhaustive at any single point in time.
Private encrypted channels aren’t covered. We can’t monitor Signal groups or private Discord servers. Data in those channels only becomes visible when it’s reposted to a source we do monitor.
The Breachsense breach tracker and the monitoring platform serve different purposes.
The tracker is a public feed of ransomware victims. It shows which companies were hit and which group claimed the attack. It’s free and updated daily.
The monitoring platform goes deeper. It indexes stolen credentials and stealer logs. You can search the contents of leaked ransomware files too. Search for your specific data and get real-time alerts.
Here’s how they connect: the tracker tells you a vendor was hit by ransomware. The platform lets you search the leaked files to see if your company’s data was in the dump.
For a detailed breakdown of how the tracker collects and verifies ransomware incidents, see how the breach tracker works.
Breachsense monitors dark web marketplaces and hacker forums 24/7. Ransomware leak sites are tracked too. We index leaked files so you can search their contents.
Our monitoring has limits. We can’t access private encrypted channels, and there’s always a gap between when the breach occurred and data surfacing publicly. We’re transparent about those gaps because your security decisions depend on knowing what your tools can and can’t see.
If you want to check your current exposure, run a dark web scan. For continuous monitoring with real-time alerts, see Breachsense dark web monitoring.
Sources are crawled continuously, not on a schedule. Automated collectors run 24/7 across all monitored source types. When new data appears on a forum or marketplace, it gets picked up and processed.
Alerts typically fire within minutes of detection. The exact speed depends on the source type. Ransomware leak site postings trigger alerts almost immediately. Stealer log processing may take slightly longer due to volume.
You tell us which domains and emails to watch. When matching credentials or session tokens show up in any monitored source, you get an alert. You can also get alerts when a vendor appears on a ransomware leak site or when a phishing domain targeting your brand is detected.
No. We only index data that’s publicly available on dark web sources. We don’t purchase stolen data or negotiate with attackers.
Coverage expands based on intelligence value and customer needs. If a specific source is relevant to your risk model, contact us. We regularly add new sources as they become active.
The breach tracker is a public feed showing which companies were hit by ransomware groups. The monitoring platform is different. You can search indexed credentials and stealer logs for your own exposed data.
The database goes back to 2007. That’s useful because some employees never change passwords, and historical matches reveal reuse patterns you’d otherwise miss.
Attack Surface Management EASM
What Are External Attack Surface Management Tools? External attack surface management (EASM) tools continuously discover …

Threat Intelligence Dark Web Monitoring
What Is Cyber Threat Intelligence Software? You can’t monitor every dark web forum and criminal channel yourself. CTI …