What is a breach protection platform?
The platform tracks criminal marketplaces and Telegram channels. It also watches paste sites and ransomware leak sites for exposed employee passwords and customer data. Relevant alerts get filtered down to the threats that actually matter to you.
According to IBM’s 2025 Cost of a Data Breach Report, breaches contained early cost about $1.1 million less than those caught late. The platform works around the clock to catch breaches early. You’ll get time to reset passwords, revoke access, and prevent account takeovers before damage occurs. Breach protection platforms also monitor your third-party vendors. When a vendor you use gets breached, you’ll often find out through monitoring before the vendor even notifies you. That early warning gives you time to assess what was exposed and lock down affected access.

Why you need a breach protection platform
Detect breaches before exploitation
Save USD 1.1 million per breach
Automate incident response
Breach Protection Platform Trusted by Security Teams Worldwide
Our team uses Breachsense data to gain initial access during pen testing and red team engagements. The API is simple to use and the support is always helpful and responds quickly.
Our Security Colony platform relies on Breachsense data as part of our dark web monitoring service. The data is continuously updated and high quality. Highly recommend!
We rely on Breachsense for a lot of data. Their frequent database updates, constant availability, and handling of big and small breaches alike means we are always covered.
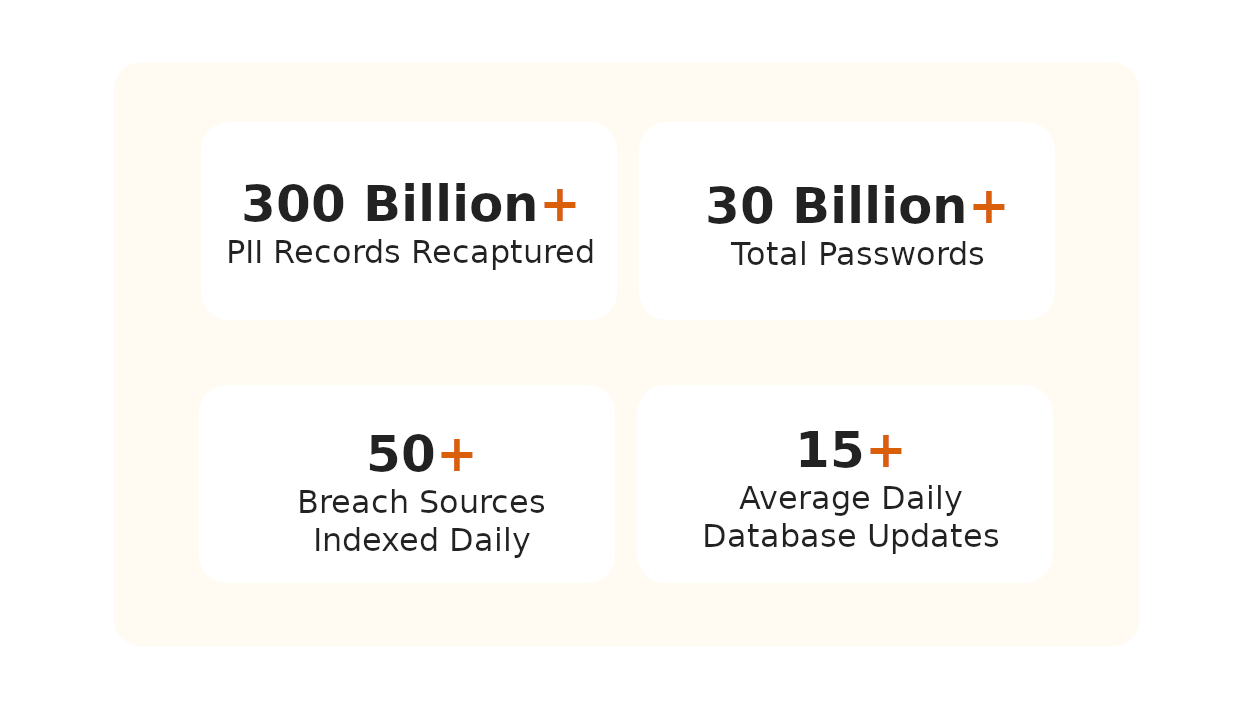
How Does Breachsense Protect Against Breaches?
Add Your Domains & Assets
We Monitor Dark Web Sources
Get Instant Breach Alerts
Shut Down Exposed Access
Frequently Asked Questions
Breach protection is a security system that protects your organization’s sensitive data from unauthorized access. It works by continuously monitoring the dark web for leaked credentials, customer information, and proprietary data. A breach protection platform alerts you instantly when your data appears in new breaches. You can then reset passwords and revoke access before attackers exploit the information. This helps prevent account takeovers and cut breach costs.
You can detect data breaches through multiple channels. Security teams spot breaches through system logs showing unauthorized access or unusual data transfers. External notifications may come from law enforcement or threat intelligence partners when your data is found in unauthorized locations. Dark web monitoring alerts you when your credentials appear on criminal marketplaces. Regular security audits and automated monitoring add another layer of detection.
Compromised credentials remain the primary attack vector for data breaches. According to Verizon’s 2025 Data Breach Investigations Report, 88% of web application breaches involved stolen or brute-forced credentials. Attackers use these leaked credentials to gain initial access to your network. Knowing which of your credentials are exposed lets you reset them before they’re exploited. Compromised credential monitoring helps prevent credential-based breaches.
You prevent data breaches through technical controls and security best practices. Core defenses include multi-factor authentication (MFA) and password managers. Network segmentation helps contain potential compromises. According to CISA cybersecurity best practices, you should implement defense-in-depth strategies. Complement these controls with continuous dark web monitoring to detect leaked credentials before exploitation. Regular penetration testing helps identify vulnerabilities before attackers exploit them.
A breach protection platform continuously monitors the dark web and third-party breaches for your exposed data. It scans criminal marketplaces and hacker forums for leaked credentials and sensitive information. When your data appears in a breach, you get instant alerts. You can then reset passwords and revoke access before attackers exploit it. Breachsense integrates with your SIEM and SOAR tools to automate incident response.
Breach protection platform costs vary based on your organization’s size and needs. Enterprise platforms typically charge based on the number of employees monitored or data volume. Pricing ranges widely depending on scope. However, breaches caught early cost about $1.1 million less than those found late (IBM’s 2025 Cost of a Data Breach Report). That makes breach protection a cost-effective investment for most companies.
When one of your vendors gets breached, your data may be exposed even though your own systems weren’t attacked. A breach protection platform monitors for your data across third-party breaches and alerts you when it appears. You’ll often find out about a vendor breach through monitoring before the vendor notifies you. This gives you time to reset affected credentials, revoke session tokens, and assess what data was exposed.
No platform can guarantee 100% breach prevention. However, breach protection platforms significantly reduce your risk by detecting compromised credentials before attackers exploit them. They monitor for leaked passwords and session tokens across the dark web. You’ll get time to respond before breaches escalate. Combined with strong authentication controls and network segmentation, you get multiple layers of defense that stop most breach attempts before they cause damage.
Essential Breach Protection Resources
Guides and tools for breach protection
Data Breach Monitoring
Continuous monitoring for third-party breaches affecting your organization. Get real-time alerts when your data appears in new breaches or leaks.
Learn MoreCompromised Credential Monitoring
Monitor for leaked employee and customer credentials across the dark web. Reset passwords before attackers exploit compromised accounts.
Learn MoreDark Web Monitoring
Track criminal marketplaces and hacker forums where stolen data is sold. Detect exposed information before cybercriminals use it against you.
Learn MoreCyber Threat Intelligence Software
Feed breach alerts into your threat intelligence workflows. Prioritize which exposures need immediate action.
Learn MoreData Breach Detection Software
Compare breach detection tools and software for enterprises. Features, capabilities, and implementation guidance for security teams.
Learn MoreCheck Your Exposure
Free scanner to check if your organization’s credentials are already on the dark web. See what breaches have exposed your data instantly.
Learn MoreWhat Is a Data Breach?
How breaches happen, common causes, and steps to protect against them.
Learn MoreData Breach Mitigation
Immediate steps to take after discovering a data breach. Minimize damage and prevent further exposure.
Learn More