Learn how to bridge the gap between collecting threat intelligence and actually preventing breaches.
• The threat intelligence lifecycle has six phases, but most teams only execute five. They skip feedback, which means they never learn what’s working. Without feedback driving requirements, your lifecycle is a straight line, not a cycle.
• Collection is the easy part. Every team can subscribe to threat feeds. The hard part is analysis: turning 2,000 daily alerts into the 3 that actually matter for your environment. If your analysts spend more time processing than analyzing, your lifecycle is broken.
• Strategic and tactical intelligence both flow through the same lifecycle but serve different audiences. Mixing them up is why CISOs get blank stares from boards and SOC analysts get reports they can’t use.
• Measure business outcomes, not activity. “We processed 50,000 IOCs” means nothing. “We detected compromised vendor credentials 3 weeks before the breach” means everything. The teams that prove ROI keep their funding.
93% of security teams have threat intelligence programs (SANS 2024 CTI Survey). Most of them still can’t answer the question: “Did our intelligence actually prevent anything?”
The problem isn’t the framework. It’s execution. Teams collect everything and prioritize nothing.
This guide walks through the six-phase threat intelligence lifecycle and shows where teams get it wrong.
What Is the Threat Intelligence Lifecycle?
The threat intelligence lifecycle is a six-phase process that turns raw threat data into decisions that prevent breaches. Without it, intelligence is reactive. You subscribe to feeds and block an IP here and there, but none of it connects to a bigger picture.
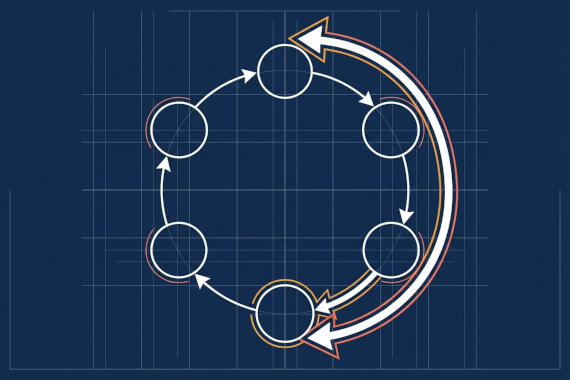
Threat intelligence lifecycle is a continuous six-phase cycle (direction, collection, processing, analysis, dissemination, feedback) that converts raw threat data into actionable intelligence. The critical word is “cycle.” Phase 6 feeds back into Phase 1, so you get better at asking the right questions over time.
The cyber threat intelligence lifecycle isn’t new. It’s adapted from military intelligence frameworks that have been refined for decades. What’s changed is how security teams apply it. The SANS 2024 CTI Survey found that while most teams have formal CTI programs, most still struggle to make intelligence actionable. The most common gap: teams document phases 1-5 but skip phase 6 (feedback), so the process never gets better.
The threat intelligence cycle matters because without structure, you collect everything and prioritize nothing. For the operational side of running a program day-to-day, see our threat intelligence management guide. Your team drowns in 2,000+ daily alerts while the one that matters gets buried. The lifecycle forces you to start with “what decisions will this intelligence inform?” instead of “what data can we collect?”
In practice, the programs that fail aren’t missing phases. They’re missing the discipline to kill feeds and reports that nobody acts on.
What Are the 6 Phases of the Threat Intelligence Lifecycle?
Here’s what each phase does and where teams tend to cut corners.
Phase 1: Direction
Direction is easy to rush past. It’s tempting to jump straight to collection without defining what you actually need. Direction means answering two questions: What assets matter most, and what decisions will this intelligence inform?
Good direction produces Priority Intelligence Requirements (PIRs). Not “collect everything about ransomware.” More like “identify ransomware groups exploiting VPN vulnerabilities in our sector and provide early warning when our credentials appear on criminal markets.”
Phase 2: Collection
Collection is the easiest phase to over-invest in. Teams subscribe to 15 threat feeds and pull OSINT from dozens of sources, generating more data than they can possibly analyze.
Better approach: collect from sources that directly answer your PIRs. That might include commercial threat feeds and internal logs. Dark web monitoring for credential exposure is another high-value source, as is ISAC sharing for industry-specific threats.
The SANS 2024 survey found 90% of teams rely primarily on external sources. That’s fine as a starting point, but don’t ignore internal data. Your own logs and incident reports contain intelligence no external feed can provide.
Phase 3: Processing
Processing turns raw data into a format your analysts can actually work with. This means deduplication and enrichment with context. If collection pulls in 50,000 IOCs, processing should reduce that to the ones relevant to your environment.
This is where data quality issues surface. The SANS survey found 41% of teams struggle with data quality. Bad processing means your analysts start with garbage, and no amount of analysis fixes that.
Automation helps here. Your threat intelligence platform should handle the mechanical work (format conversion and enrichment lookups) so analysts spend time on analysis, not data cleaning.
Phase 4: Analysis
Analysis is the phase that separates intelligence from data. It answers “so what?” and “what should we do about it?”
Good analysis: “Three IPs associated with a ransomware group’s C2 infrastructure attempted connections to our VPN gateway in the last 48 hours. Block these IPs and review VPN access logs for successful authentications from unusual locations.”
Bad analysis: “10,000 malicious IPs detected this month. Continue monitoring.”
The first drives action. The second creates busywork. If your analysis doesn’t end with a recommendation someone can act on, it’s still just data.
Phase 5: Dissemination
Get the right intelligence to the right people in a format they can actually use. Your CISO doesn’t need a list of IOCs. Your SOC analysts don’t need a board-level risk summary.
Strategic intelligence goes to executives in business language with dollar figures. Operational intelligence goes to SOC managers with campaign context and recommended mitigations. Tactical intelligence goes to analysts as IOCs plus detection rules they can deploy immediately.
A common pitfall: producing one report for everyone. A single report can’t serve a board member and a SOC analyst simultaneously. Format intelligence for each audience.
Phase 6: Feedback
Feedback is the phase that gets deprioritized when things get busy. It’s also the phase that makes everything else work.
Feedback means asking: Did this intelligence help you make a decision? Did you act on it? What gaps remain? What intelligence did you need but didn’t get?
Most teams skip this step entirely, which is why the same useless report gets generated next quarter. Without feedback, the process stagnates. You end up collecting the same data and producing reports that don’t evolve with your needs. With feedback, you learn what’s worth collecting and what’s noise. That’s what makes it a cycle instead of a straight line.
What Are the Types of Threat Intelligence?
The types of threat intelligence flow through the same lifecycle, but each one serves a different audience.
Indicators of Compromise (IOCs) are technical artifacts like IP addresses and file hashes that indicate a system may have been breached. SOC analysts use IOCs from tactical intelligence to detect and block threats in real time.
Strategic intelligence serves CISOs and board members making decisions over months to years. It answers business questions: “Third-party breaches now account for 30% of all incidents. Should we increase our vendor security budget?” This is the intelligence type that justifies funding.
Operational intelligence serves SOC managers and threat hunters over weeks to months. It provides campaign context: “This ransomware group is targeting healthcare companies through Citrix vulnerabilities. Here are the TTPs and recommended mitigations.”
Tactical intelligence serves SOC analysts in real time. It provides IOCs and detection rules to block threats immediately. It has the shortest shelf life because IP addresses and domains change constantly.
The mistake most teams make: collecting only tactical intelligence while neglecting the strategic work. Tactical intelligence blocks today’s threats. Strategic intelligence prevents next year’s breaches. Your lifecycle needs to produce both.
Where Do Most Teams Get the Lifecycle Wrong?
Knowing the phases is straightforward. These are the patterns that trip teams up in practice.
Collecting Everything, Analyzing Nothing
It’s easy to fall into this one. You subscribe to every available feed and ingest millions of IOCs. Your analysts drown. More data doesn’t equal better intelligence. If your analysts spend 80% of their time processing and 20% analyzing, your ratio is backwards.
Fix: ruthlessly match collection to your PIRs. Drop feeds that consistently produce false positives or intelligence you never act on.
Skipping Requirements
This is the Direction phase problem from above, but it’s worth repeating because it’s so common. If you didn’t define what questions intelligence should answer, the CISO asks “what’s our biggest risk next year?” and nobody can answer.
Fix: start each cycle with stakeholder interviews. Ask what decisions they need intelligence to inform.
One Report for Every Audience
A board member and a SOC analyst need completely different intelligence. A single monthly report can’t serve both. Board members get bored by IOCs. Analysts can’t act on risk summaries.
Fix: build separate dissemination tracks. Strategic briefs go to executives. Operational summaries go to SOC managers. Tactical feeds push directly into security tools.
Ignoring Internal Intelligence
90% of teams rely primarily on external sources. External feeds tell you what’s happening across the internet. Your own logs and incident history tell you what’s happening in your environment. The combination is where real intelligence lives.
No Feedback Loop
Without Phase 6, you don’t know what’s working. If nobody tells you the weekly report isn’t useful, you’ll keep producing it. Regular feedback is what turns a static process into one that actually gets better over time.
How Do You Measure Whether Your Intelligence Program Works?
Proving value keeps your program funded. Here’s how to measure what matters.
Business outcome metrics matter most. Track breaches prevented with estimated dollar values. Track how intelligence informed budget decisions. Track mean time to detect (MTTD) and whether it’s getting faster.
Operational metrics show whether the lifecycle is running smoothly. Alert volume and false positive rate (target under 40%). Also track how much analyst time goes to processing vs. analysis.
Feedback metrics close the loop. Are stakeholders acting on intelligence? Which reports get read and which get ignored? What intelligence gaps caused your last incident?
Bad metric: “We processed 50,000 IOCs this month.”
Good metric: “Intelligence-driven detection caught compromised credentials 3 weeks before they were used. Estimated cost avoidance: $4.44M based on average breach costs (IBM 2025).”
The first measures activity. The second measures impact.
How Does Dark Web Monitoring Fit Into the Lifecycle?
Dark web monitoring maps directly to the collection and analysis phases. It catches attackers before they reach your network, which makes it one of the most useful sources you can plug into the lifecycle.
In the collection phase, credential monitoring scans criminal markets and infostealer logs for your company’s exposed credentials. This is intelligence most external feeds don’t provide because it requires direct access to dark web sources.
In the analysis phase, discovering your vendor’s credentials for sale on a criminal market is tactical intelligence (reset those passwords now) and strategic intelligence (your third-party risk program has gaps). The same data point drives both immediate action and long-term policy changes.
In the feedback phase, you can measure: How many compromised credentials did we catch? How quickly did we reset them? Did any get exploited before we acted? Those metrics prove the value of your monitoring investment.
This is where the lifecycle connects to prevention. Stolen credentials circulate on dark web markets for days or weeks before attackers use them. Catching them during that window prevents the breach entirely.
Conclusion
The threat intelligence lifecycle is a framework most teams have on paper but few execute well. The difference between the teams that succeed and everyone else comes down to a handful of habits.
Start with requirements. If you don’t know what decisions intelligence should inform, you’ll collect data nobody uses.
Close the feedback loop. Phase 6 is what makes the lifecycle a cycle. Without it, you’re running the same broken process on repeat.
Measure outcomes, not activity. Show how intelligence prevented a breach or informed a budget decision.
One more thing worth saying out loud: the tension between tactical speed and strategic depth is real, and pretending otherwise is how programs lose the plot. You need fast IOC delivery for the SOC, and you need slow, well-researched strategic reports for the board. The same analyst can’t do both on the same day. Staff accordingly.
Book a demo to see how Breachsense feeds dark web credential intelligence directly into your threat intelligence lifecycle.
Threat Intelligence Lifecycle FAQ
The threat intelligence lifecycle is a six-phase process (direction, collection, processing, analysis, dissemination, feedback) that turns raw threat data into intelligence your team can act on. The key word is ‘cycle.’ Phase 6 (feedback) feeds back into Phase 1 (direction), so your requirements get sharper over time.
Raw data tells you an IP address is malicious. Intelligence tells you it’s part of a ransomware group’s C2 infrastructure targeting your industry through VPN exploits, plus how to find them in your logs. Context and actionability are what separate intelligence from data dumps.
Strategic intelligence helps executives make budget and policy decisions (months-to-years timeframe). Operational intelligence helps SOC managers understand active campaigns (weeks-to-months). Tactical intelligence gives analysts specific IOCs to block threats immediately (hours-to-days). Each type serves a different audience.
NIST’s Cybersecurity Framework aligns with the lifecycle at multiple points. The Identify function maps to the direction phase. Detect maps to collection and analysis. Respond maps to dissemination. The lifecycle provides a more granular process for the intelligence activities NIST describes at a higher level.
Yes. Smaller teams actually have an advantage: fewer silos and faster decisions. Start with 2-3 high-quality sources that match your biggest risks. You don’t need 15 threat feeds. You need the right intelligence reaching the right people.
Track business outcomes, not volume. How many breaches did intelligence help prevent? How much faster do you detect threats compared to last quarter? Did intelligence inform a budget decision? If you’re counting IOCs processed, you’re measuring the wrong thing.