Deep Web vs Dark Web: Understanding the Difference
Threat Intelligence Educational Content
What Is the Difference Between the Deep Web and Dark Web? The internet has three layers. Each one works differently and …
Threat Intelligence Educational Content
What Is the Difference Between the Deep Web and Dark Web? The internet has three layers. Each one works differently and …

Data Breach Incident Response Credential Theft
What Is Data Theft? When attackers break in, they’re not just looking around. They’re taking what they came for. Unlike …
Email Security Dark Web Monitoring
What Does It Mean if Your Email Is Found on the Dark Web? Finding your email on the dark web is more common than you’d …

Threat Intelligence Security Tools SOC Operations
Threat intelligence feeds are the foundation of automated threat detection. They provide the indicators your security …

What Happened in the Home Depot Data Breach? The Home Depot data breach was one of the largest retail security incidents …
Data Breach Threat Intelligence
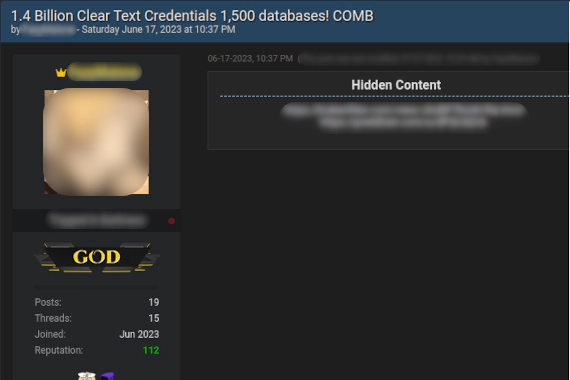
What Is A Password Combo List? Combo List: A file containing username and password pairs collected from data breaches …
What Happened in the Equifax Data Breach? The Equifax breach started with a web application vulnerability that had been …
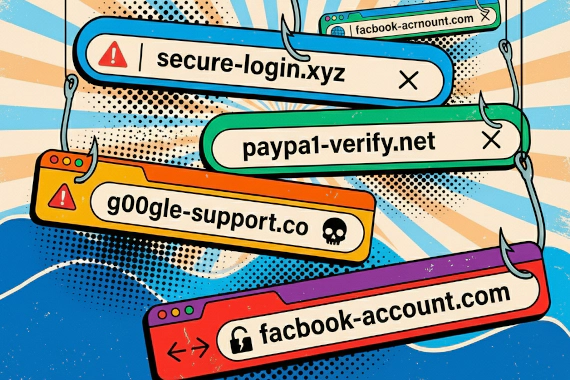
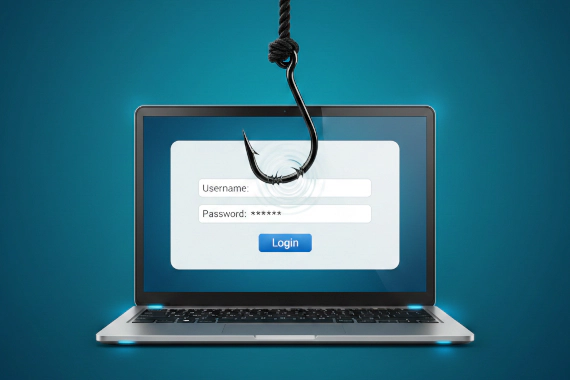
Phishing Domain Security Typosquatting Brand Protection
What Is Phishing? Phishing is a social engineering attack where criminals impersonate trusted entities to steal …

Dark Web Tor Browser Privacy Anonymity Cybersecurity
What Is the Dark Web? The dark web is a small encrypted portion of the internet requiring special browsers to access. It …

Supply Chain Security Third-Party Risk Data Breaches Vendor Risk Management Dark Web Monitoring
What Is a Supply Chain Attack? Your vendors have keys to your kingdom. When attackers steal those keys, they walk right …
Data Breach Case Studies Telecom Security Network Security
What Happened in the T-Mobile Data Breaches? T-Mobile has disclosed at least seven significant data breaches since 2018. …

Vendor Risk Management Third-Party Risk Supply Chain Security Dark Web Monitoring
What Is Vendor Risk Management? Your vendors have access to your data. When they get breached, your data gets exposed …