
What to Do if Your Company's Information Is Found on the Dark Web
Dark Web Monitoring Identity Theft
What Kind of Data Ends Up on the Dark Web? When your company’s data appears on the dark web, it usually falls into a few …

Dark Web Monitoring Identity Theft
What Kind of Data Ends Up on the Dark Web? When your company’s data appears on the dark web, it usually falls into a few …

Data Security Credential Protection Network Security Threat Prevention
What Is Data Interception? When security teams think about data interception and theft, they usually picture someone …

What Is a Data Leak? A data leak happens when sensitive information gets exposed without anyone intending it to. No …
Risk Management Data Security Best Practices
What Is a Data Risk Assessment? You can’t protect data you don’t know about. A risk assessment tells you what you have, …

Data Security Best Practices Compliance
What is a Data Security Audit? If you don’t audit your security regularly, you’re trusting that nothing has changed …
Credential Stuffing Authentication Security
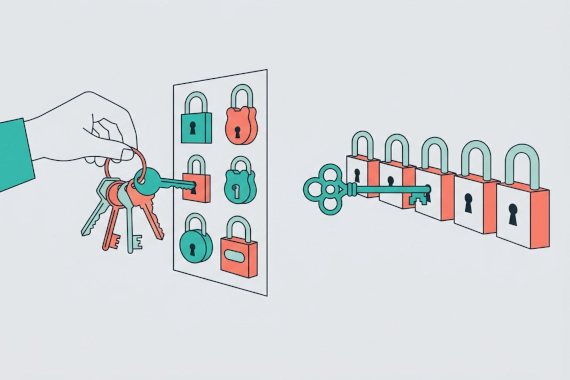
What Is Credential Stuffing? Credential stuffing is one of the most common account takeover methods. You’ve probably …
Credential Stuffing Account Takeover
What Is Credential Stuffing? Password reuse creates a massive security hole. When you use the same password on multiple …

How Much Does a Data Breach Cost? The global average cost of a data breach dropped to $4.44 million in 2025, down from …

What Is Big Data Security? If you’re running Hadoop clusters or cloud data lakes, you already know that standard …

Email Security Credential Theft
What Is Business Email Compromise? BEC is one of the most expensive cyber threats, and it doesn’t involve any malware or …

Credential Monitoring Dark Web Monitoring Data Breach
Why Should Security Teams Check Employee Credentials? Most security teams focus on blocking attacks. But what happens …

1. Yahoo Date: August 2013 Impact: 3 billion records Yahoo holds the record for the largest data breach in history, and …