The Breachsense 2025 Dark Web Exposure Report
Learn what attackers actually stole in 2025 and what to change about your defense for 2026.
• Infostealer infections added 1.56 billion fresh credentials to the Breachsense corpus in 2025, averaging 547 saved passwords per infected machine. One laptop can expose hundreds of your accounts.
• 86% of the credentials in our pipeline are available as plaintext. We don’t just find the hash. We give you the plaintext password.
• Ransomware claimed 7,307 unique victims across 138 operators in 2025, up 45% YoY. Qilin (958) overtook CL0P as the volume leader. The ecosystem got bigger and more fragmented, not smaller.
• AI tool credentials hit the mainstream stealer log market: 1.02M OpenAI entries, HuggingFace +18% YoY. Rotate and monitor AI tokens the same way you treat Slack or GitHub access.
• “Biggest breach of 2025” is no longer a meaningful concept. Aggregator postings repackage years of historical data. Volume is not a quality signal.
Most annual threat reports inflate their headline totals by blending fresh compromises with recycled combolist data. This one doesn’t.
This report draws only from sources where our discovery timestamps reflect when data actually entered the criminal underground. Stealer logs, sessions, ransomware leak sites, hacker forum chatter, and net-new third-party breaches added to our pipeline.
If you evaluate threat intelligence vendors on credential volume alone, you are paying for the same data multiple times. What actually matters is coverage across stealer logs, combolists, third-party breaches, session tokens, exposed databases, ransomware leak files, hacker forums, and Non-Human Identity tokens.
Here is what we saw in 2025, what changed, and how to think about your defense in 2026.
What 2025 actually looked like
Breachsense has indexed 90+ billion identity records across third-party breaches, combolists, infostealer logs, and stolen session cookies. This report is about what we added to that corpus in 2025, measured at the source where we can cleanly distinguish fresh compromises from recycled aggregator data.
In 2025 alone, infostealer infections gave us 1.56 billion fresh credentials. Across 138 ransomware operators, we tracked 7,307 unique claimed victims. Across the Telegram channels and gated forums where breach data is first traded, we recorded 53,433 distinct mentions of victim domains and trade activity.
One number that does not depend on when data arrived: 86% of the credentials in our third-party breach corpus are available as plaintext, and combolist and stealer-log sources arrive as plaintext natively. We don’t just find the hash. We give you the plaintext password. A hash collision triggers a guess. A plaintext match triggers action.
Here is the full 2025 exposure surface.
| Metric | 2025 | YoY |
|---|---|---|
| Total corpus (cumulative) | 90+ billion identity records | n/a |
| Stealer credentials captured | 1.56 billion | +7% |
| Plaintext across breach corpus | 86% | Cracking differentiator |
| Unique infected machines | 2.85 million | -33% |
| Cookies harvested | 1.07 billion | -20% |
| Ransomware victims claimed | 7,307 | +45% |
| Avg credentials per infected machine | 547 | yield up YoY |
| Net-new third-party breaches added | 193 | spread across every month |
Fewer infections, more credentials per infection. Unique infected machines dropped 33% YoY while the stealer-credential total grew 7%. Average yield climbed from 344 saved passwords per machine in 2024 to 547 in 2025. Infostealer malware is pulling more saved passwords on each run.
Infostealer analysis
The infostealer ecosystem consolidated in 2025 even as raw infection counts dropped. Five families produced 92% of the credentials we ingested. “Stealer logs” and “infostealers” show up throughout this report. Here is what we mean.
Stealer logs are the data dumps produced by infostealer malware after it runs on a victim’s machine. A single log contains every saved password the malware could extract from the browser’s credential database, plus session cookies, credit card numbers, crypto wallet files, and system metadata. Stolen logs are sold in bulk on criminal markets and private Telegram channels. One infected employee laptop typically yields hundreds of credentials across corporate and personal services.
Here is how the 2025 infostealer market broke down by family.
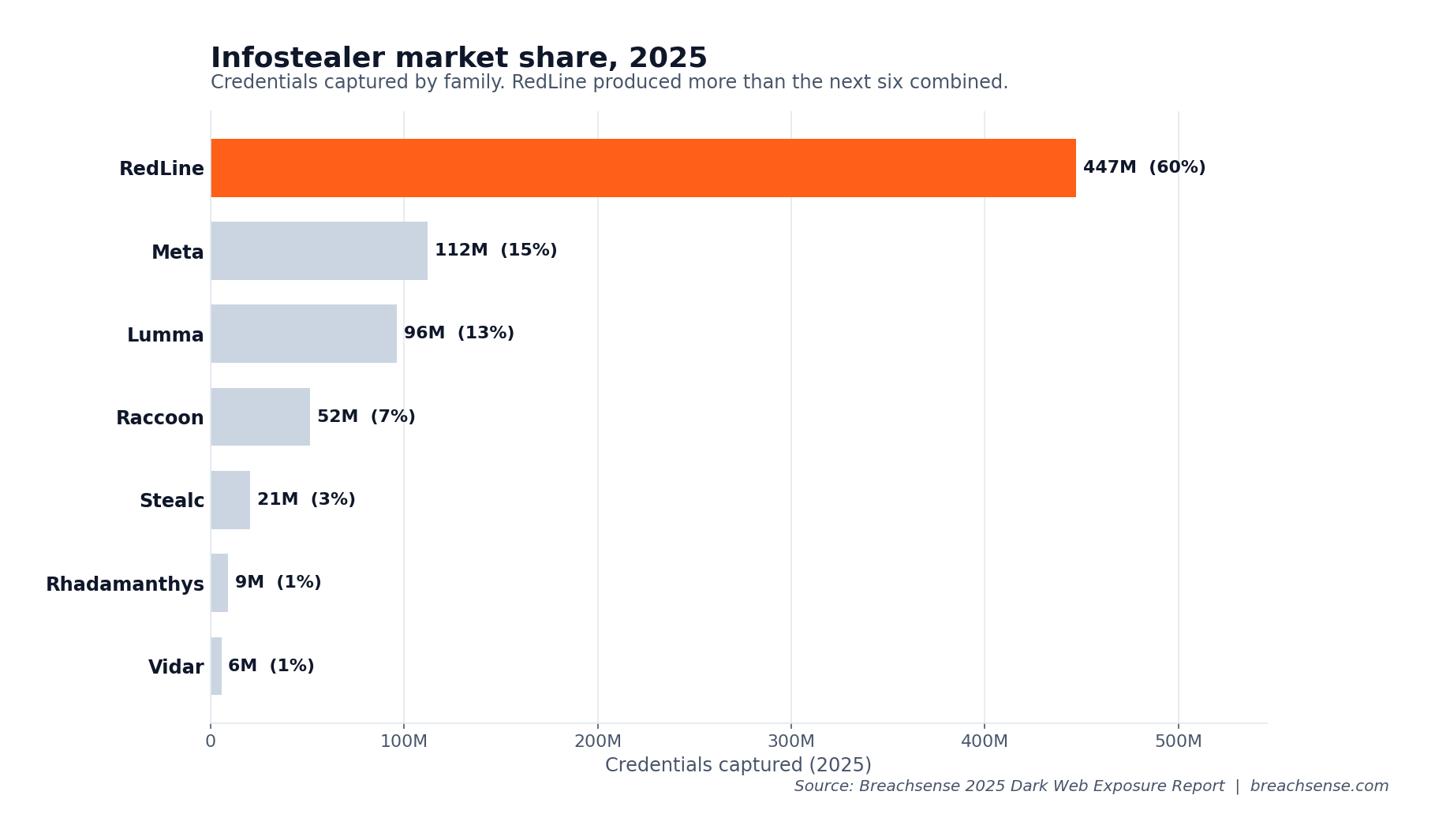
The per-family counts show just how far ahead RedLine sits.
| Family | 2025 credentials |
|---|---|
| RedLine | 447,328,864 |
| Meta | 112,127,528 |
| Lumma | 96,407,466 |
| Raccoon | 51,520,641 |
| Stealc | 20,504,752 |
| Rhadamanthys | 9,053,976 |
| Vidar | 5,675,383 |
RedLine alone accounted for 447 million credentials, almost three times its nearest rival. Meta Stealer (a RedLine fork that picked up volume after RedLine’s law enforcement disruption) reached 112 million. Lumma at 96 million held its position despite a partial takedown announcement mid-year. Raccoon and Stealc rounded out the top five.
Other researchers have reported Lumma surpassing RedLine in H2 2024. Our collection still shows RedLine ahead by both credential volume and unique infection count through 2025, likely reflecting source-channel differences. Per infection, Lumma is more efficient than RedLine in our data (331 credentials per infected machine vs 198).
The volume curve is volatile. January through April held at 80-100 million credentials per month. June spiked to 231 million as a major operator dumped backlog. September hit 308 million on the back of a Lumma-affiliate distribution wave. Then the curve collapsed.
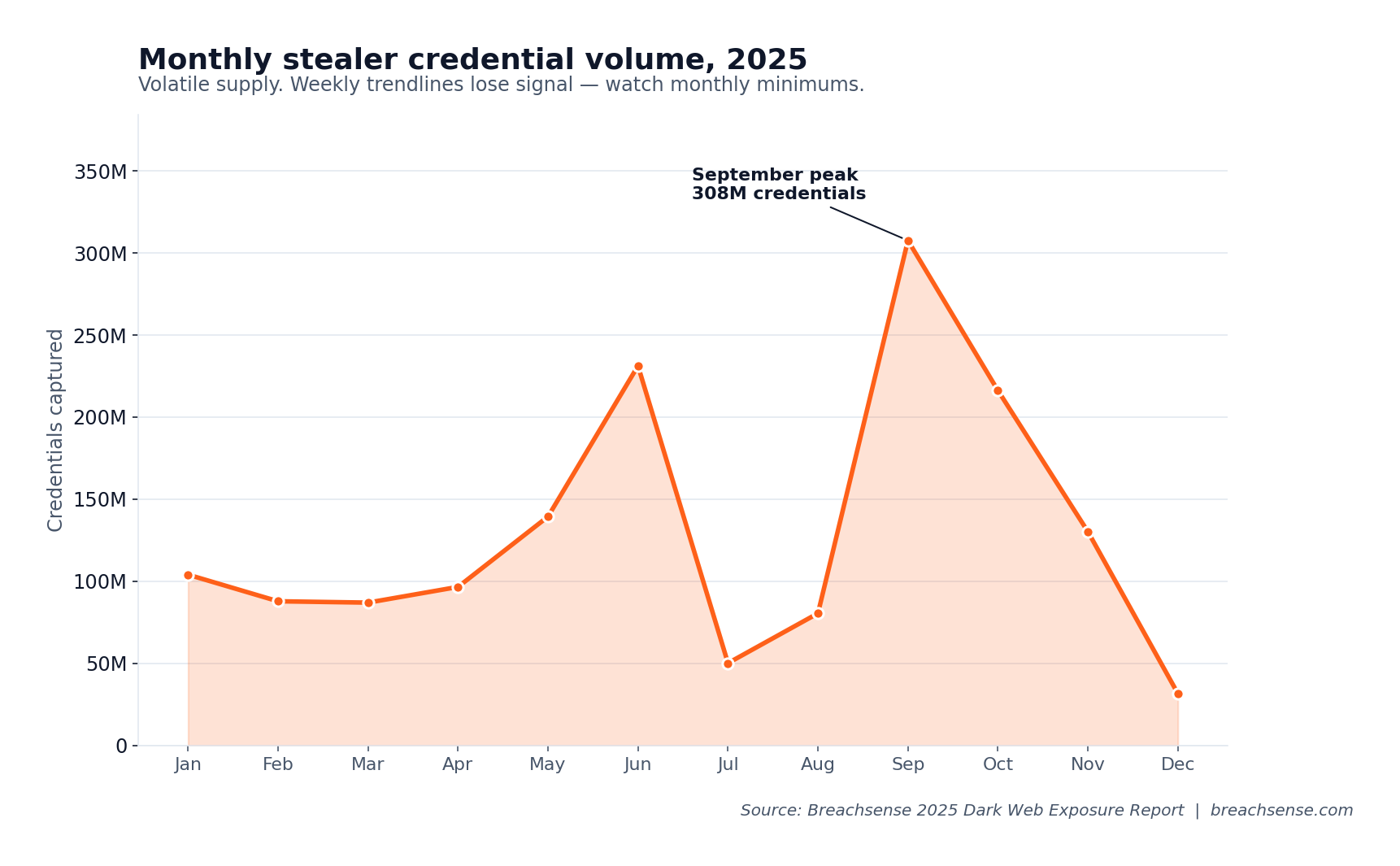
Weekly trend lines miss this. Watch monthly minimums instead.
AI tools are now in the credential market
OpenAI credentials appeared in 1,019,776 stealer log entries in 2025. The 2024 figure was 1.51 million, so our absolute count is down 33% YoY. That tracks the broader infection drop, not any reduction in AI-platform exposure per machine. Here is the full platform ranking.
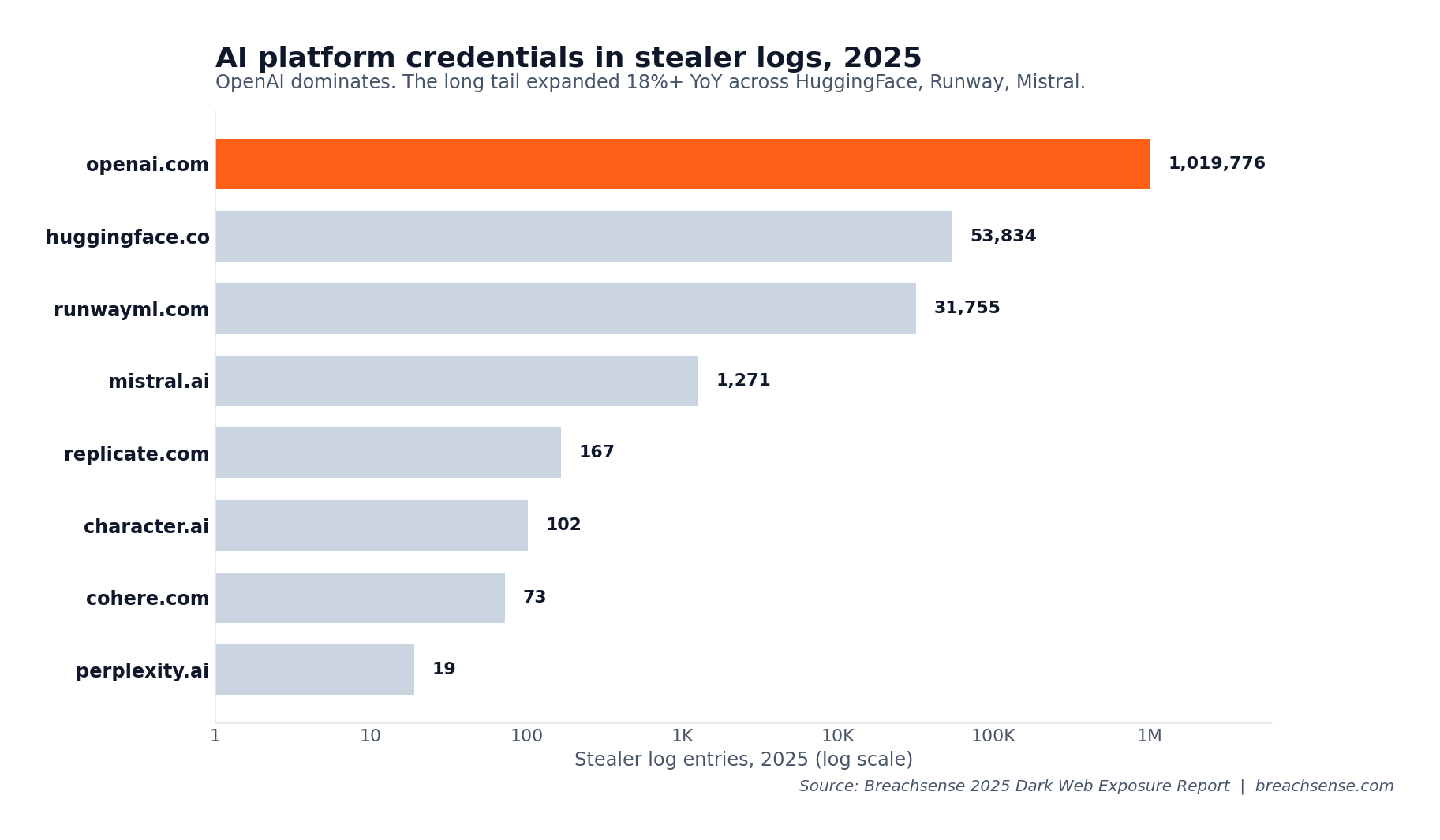
Although OpenAI dropped, every smaller platform grew. The YoY breakdown:
| AI platform | 2024 entries | 2025 entries | YoY |
|---|---|---|---|
| openai.com | 1,512,870 | 1,019,776 | -33% |
| huggingface.co | 45,778 | 53,834 | +18% |
| runwayml.com | 32,241 | 31,755 | -1% |
| mistral.ai | 231 | 1,271 | +450% |
| replicate.com | 43 | 167 | +288% |
| character.ai | 18 | 102 | +467% |
| cohere.com | 63 | 73 | +16% |
| perplexity.ai | 6 | 19 | +217% |
The expansion is in the long tail. HuggingFace exposure grew 18% YoY. Runwayml hit 31,755. Mistral and Replicate appeared in four-figure counts where they previously had near-zero presence.
The takeaway for security teams: AI tool sessions are now first-class assets. Rotate OpenAI API keys when employees leave, and audit Copilot and Gemini access through your identity provider’s sign-in logs (Entra ID and Google Workspace) rather than the AI platform dashboards, which mostly don’t expose per-access IP data. Platforms that rely on SSO don’t show up as their own domain in stealer logs; the exposure path is the identity provider’s cookies, which already appear in the top session-cookie targets later in this report.
Password managers are an attack surface, not just a defense
Password manager credentials appeared in stealer logs more often than most security teams would think.
| Password manager | 2025 stealer log entries |
|---|---|
| proton.me | 149,100 |
| lastpass.com | 51,322 |
| bitwarden.com | 17,407 |
| 1password.com | 6,744 |
| keepersecurity.com | 2,580 |
| roboform.com | 2,354 |
| dashlane.com | 1,621 |
| nordpass.com | 504 |
When the vault itself is the prize, recovery is brutal. A stolen master credential paired with a stolen browser cookie lets an attacker pull the entire vault and log into every site stored inside it, before you spot anything unusual on any one service. Enforce phishing-resistant authentication for password manager access. Rotate vault master passwords whenever an employee’s machine is suspected of compromise, not just when stealer log evidence surfaces.
Non-Human Identity exposure
Non-Human Identities (NHIs) became a distinct risk category in 2025. We track NHI exposure through stealer log captures of platform credentials, cookies, and tokens. We observed millions of NHI-adjacent records across cloud infrastructure, developer platforms, package repositories, AI APIs, and collaboration suites.
Non-Human Identities (NHIs) are the API keys, service tokens, and machine credentials that let scripts and automated systems authenticate without a person. They have no MFA, are long-lived (weeks to years), carry broad permissions because rotation is operationally painful, and detection depends on spotting unusual usage patterns.
| Category | Platform | 2025 entries |
|---|---|---|
| Developer platforms | github.com | 1,448,873 |
| Developer platforms | gitlab.com | 43,003 |
| Developer platforms | atlassian.net | 25,450 |
| Developer platforms | bitbucket.org | 12,850 |
| Package repositories | npmjs.com | 16,774 |
| Package repositories | pypi.org | 4,092 |
| AI platforms | openai.com | 1,019,776 |
| AI platforms | huggingface.co | 53,834 |
| AI platforms | runwayml.com | 31,755 |
| Collaboration | discord.com | 7,249,938 |
| Collaboration | slack.com | 134,109 |
| Container / build | docker.com | 92,453 |
Cloud-provider consoles (aws.amazon.com, portal.azure.com, console.cloud.google.com) don’t appear in the table above because cloud auth doesn’t go through the browser password store. The exposure path is the CLI credential files (.aws/credentials, ~/.config/gcloud/, Azure tokens) that stealers pull off disk alongside browser data. A compromised employee laptop with stored CLI credentials is your cloud’s most likely exposure vector.
NHIs deserve attention because they break every mitigation we built for human accounts. A single stolen NPM token lets an attacker publish a malicious package version that every downstream install pulls automatically. No MFA challenge, no login alert, no human in the loop to slow them down.
What counts as a fresh 2025 breach
Most threat-intel reports publish a “billions of new records” headline alongside a list of largest breaches. We’re explicitly not doing that this year, because the data does not support it.
The largest credential collections that surfaced in 2025 were aggregator postings. ALIEN TXTBASE, for example, was publicly disclosed in February 2025 as a 23-billion-record combolist, but the underlying data was years of repackaged breach dumps and stealer logs. Our sampling of these aggregator compilations consistently shows most of what they ship has appeared somewhere before, frequently in our own stealer log archive from months or years earlier.
That makes “credentials added in 2025” a low-quality signal of fresh compromise. Two billion records labeled as a “new breach” might be 90% recycled.
What we can confirm as net-new: 193 fresh third-party breaches were added to the Breachsense pipeline in 2025, spread across every month of the year. Smaller per-breach record counts. Real new compromise activity. None of them produce a billion-record headline.
The practical vendor question to ask: what percentage of your “new” credentials overlap with infostealer logs you already collected? If the vendor cannot answer it, the volume number isn’t measuring what they want you to think it measures.
Stolen cookies and session hijacking
We harvested 1.07 billion cookies in 2025. Most are tracker and analytics junk, but the auth-session subset is the new stolen passwords.
Session cookies bypass MFA because the authentication already happened on the victim’s machine. Cookies bypass passkeys because the FIDO assertion was already performed. A defender has three bad options to invalidate a stolen cookie. Detect the theft (rarely happens). Force a session reset (operationally costly). Or wait for natural expiration, which can take weeks or months for “remember me” tokens.
The targets are overwhelmingly enterprise SaaS. Here is where the 2025 cookies pointed.
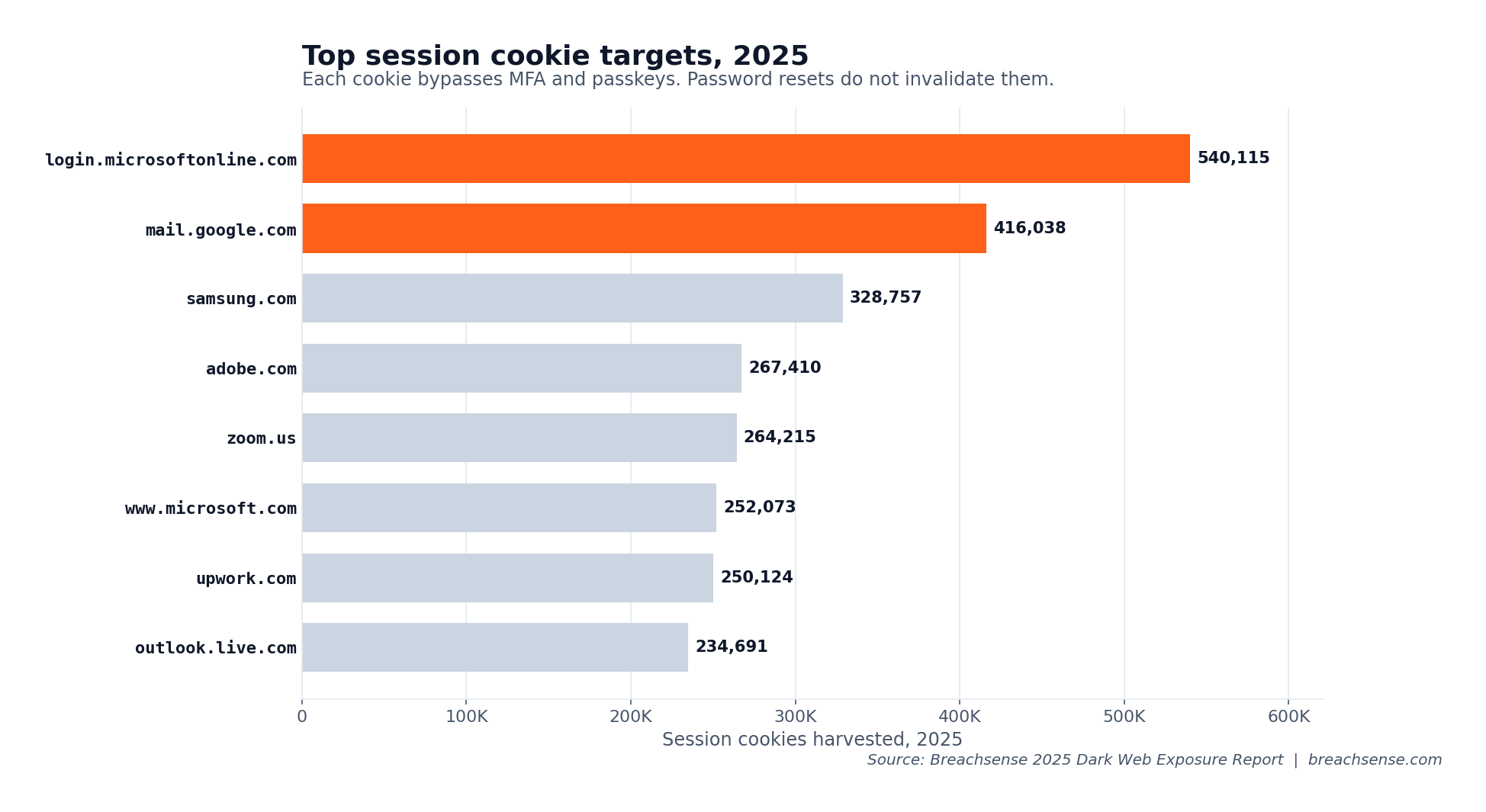
Here is the per-domain breakdown with the business context for each service:
| Target domain | 2025 stolen cookies | Why it matters |
|---|---|---|
| login.microsoftonline.com | 540,115 | Entra ID and Microsoft 365 sessions |
| mail.google.com | 416,038 | Workspace mail sessions |
| samsung.com | 328,757 | Corporate device portals |
| adobe.com | 267,410 | Creative Cloud and asset management |
| zoom.us | 264,215 | Conferencing sessions |
| www.microsoft.com | 252,073 | Microsoft account access |
| upwork.com | 250,124 | Contractor accounts inside enterprises |
| outlook.live.com | 234,691 | Personal Outlook (often used for work) |
The highest-value cookies target enterprise SaaS: Entra ID / Microsoft 365 logins, Google Workspace mail, Adobe Creative Cloud, Zoom, and contractor platforms like Upwork. If even one of those cookies belongs to a high-value SaaS tenant in your environment, you have an active session-hijacking risk that no password reset will fix.
Ransomware activity
We tracked 7,307 unique companies claimed on ransomware leak sites across 138 operators in 2025. That’s up 45% from 5,028 in 2024. More victims. More groups. More fragmentation.
The leaderboard itself turned over. Qilin took the top spot, and the 2024 leaders collapsed.
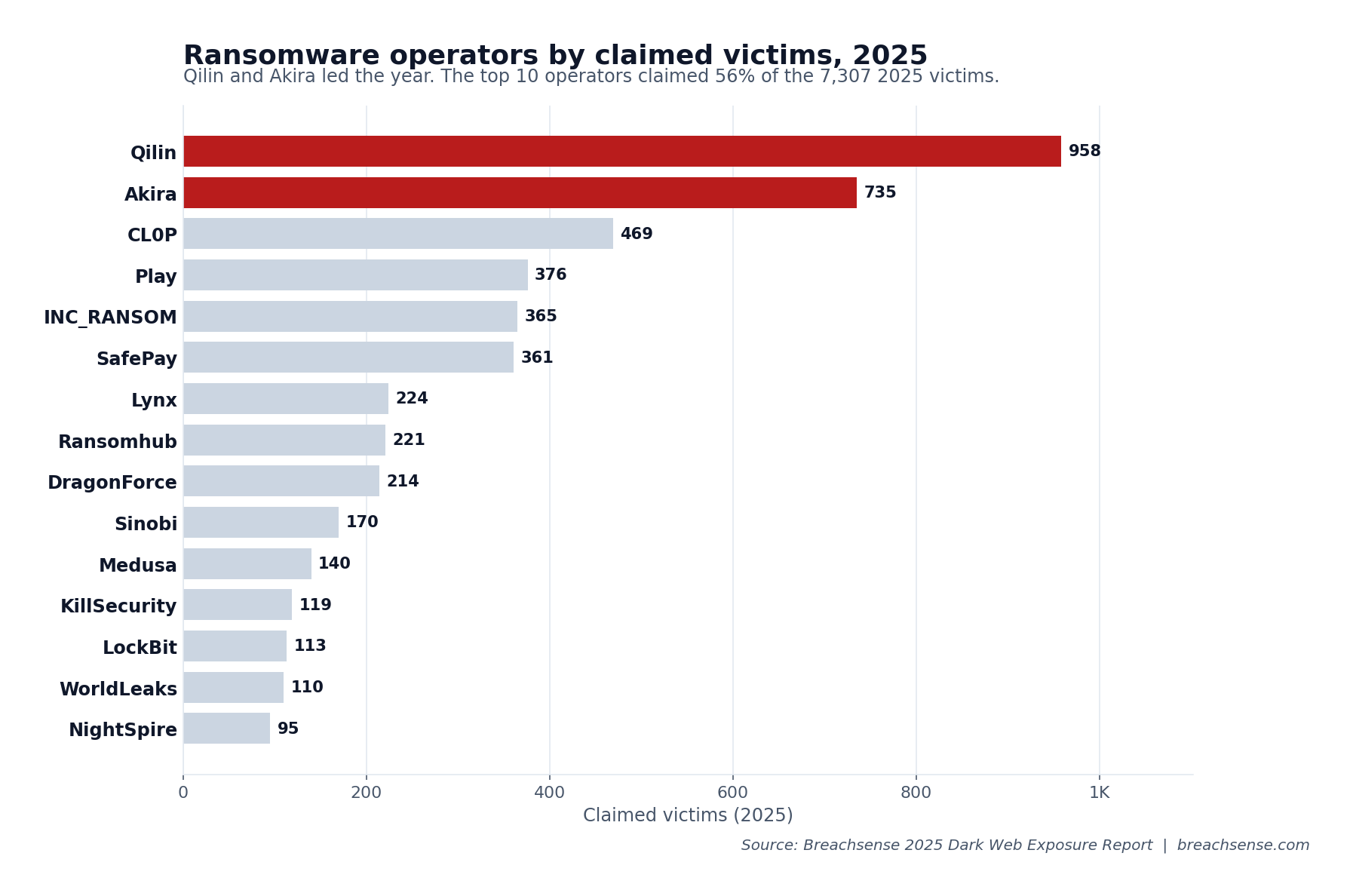
Here’s the full top-15 roster:
| Group | 2025 victims |
|---|---|
| Qilin | 958 |
| Akira | 735 |
| CL0P | 469 |
| Play | 376 |
| INC_RANSOM | 365 |
| SafePay | 361 |
| Lynx | 224 |
| Ransomhub | 221 |
| DragonForce | 214 |
| Sinobi | 170 |
| Medusa | 140 |
| KillSecurity | 119 |
| LockBit | 113 |
| WorldLeaks | 110 |
| NightSpire | 95 |
Qilin’s jump from 9th place in 2024 to first in 2025 is the year’s biggest shift. They claimed 958 victims, a 474% increase on their 2024 total. Ransomware-as-a-service affiliates moved to Qilin after Operation Cronos broke affiliate trust in LockBit and after law-enforcement pressure degraded Ransomhub.
LockBit itself fell from 513 claimed victims in 2024 to 113 in 2025. Ransomhub halved from 508 to 221. The 2024 top of the leaderboard no longer exists. For industry targeting and country breakdowns, see our State of Ransomware 2025.
Stepping back from group-by-group turnover, here’s how claim volume distributed across the year.
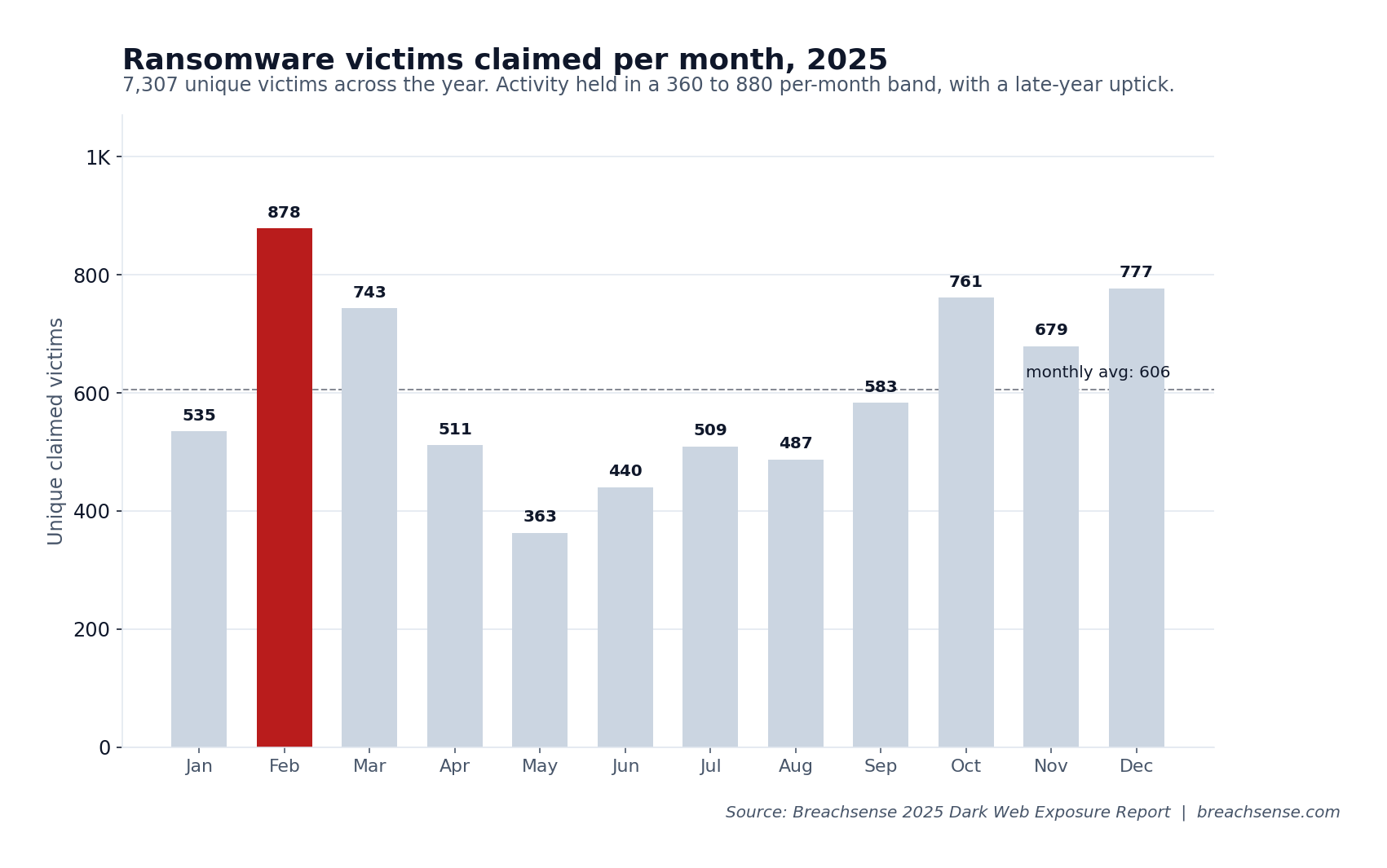
February’s 878-victim peak came from CL0P publishing its Cleo MFT victim list in one burst. May’s 363 was the low point. Between the extremes, the ecosystem never went quiet. Q4 ran consistently above average with October, November, and December all above 670. The narrative of “ransomware is slowing down” is not what the data shows.
Forums and leaked documents
Unlike scrapers and OSINT tools, Breachsense operates inside the private Telegram channels and gated forums where this data is first traded. The hacker forums themselves were in flux all year. BreachForums kept reappearing on new TLDs after repeated takedowns (breachforums.st, breached.sh, breachsta.rs, breachforums.hn), and DarkForums (darkforums.hn) emerged as a separate forum picking up displaced traders. Registration is free on all of them, but the fresh, high-value data is for sale. Individual sellers post it, negotiate privately, and never share it in the open threads. We maintain coverage across every forum.
Beyond credential data, we captured 270,054 documents from 2025 ransomware leaks and third-party breaches through our document extraction pipeline. The same pipeline indexes content from exposed Elasticsearch instances and misconfigured cloud storage. Every extracted document becomes full-text searchable, so you can query for a company name, an employee name, or any string across the full index. The largest 2025 concentrations: 221,006 from fursan.com.sa, 25,406 from a Qatar National Bank leak, 16,682 from lexipol.com. These documents drive the second-order extortion that follows initial encryption.
What this means for your defense in 2026
The 2025 data shows where attackers are getting in. Here’s what to do about each exposure category.
Credentials
1.56 billion fresh captures and an 86% plaintext corpus make the credential path the lowest-hanging fruit.
- Monitor your workforce credentials against fresh breach data and stealer logs continuously. Attackers act on fresh stealer logs within hours, so a monthly scan catches the exposure weeks after it’s been used.
- Match against cracked plaintext where possible, so a hit is a real reset instead of a guess based on a hash collision.
- Enforce phishing-resistant MFA for every workforce account. When a stealer log shows credentials from an employee’s laptop, force a password reset on every account the browser had saved.
Session cookies
Stolen enterprise-SaaS cookies bypass MFA and passkeys entirely. A password reset does not invalidate them. The top 2025 targets were Entra ID (540K captured), Google Workspace mail (416K), and Adobe, Zoom, and Microsoft accounts in the hundreds of thousands each.
- Pull stolen cookies off the criminal markets and invalidate them before attackers weaponize them (the Breachsense sessions endpoint surfaces them early).
- Enable session binding in your identity provider so tokens expire when users switch networks or devices.
- Audit active sessions for unusual sign-in patterns at the IdP level, especially for Entra ID and Google Workspace.
Non-Human Identities
GitHub, NPM, Slack, Docker, and AI platform tokens showed up by the millions in 2025 stealer logs. These break every mitigation built for human accounts.
- Inventory your NHIs. Who owns each API key, how is it scoped, when was it last rotated.
- Monitor stealer log captures for your developer tokens across GitHub, NPM, and the platforms your pipelines depend on.
- Automate rotation on exposure. Webhook into the platform’s API when a token appears on criminal markets, rather than waiting for a ticket to route.
Third parties and supply chain
193 fresh third-party breaches entered the Breachsense pipeline in 2025, spread across every month of the year. Most were smaller vendors that never made the news. Every one of them is a potential foothold if a stolen credential from that vendor was reused inside your environment.
- Extend credential monitoring to your key vendors and high-risk third parties, not just your own domain. See our supply chain monitoring overview.
- Remediate historical exposures as aggregator postings recycle them under new labels. Old credentials still get reused.
- Track hacker forum and Telegram chatter about your vendors before public leaks surface (Breachsense radar catches the conversation that precedes the listing).
The shift
Stealer logs and stolen session cookies aren’t edge cases anymore. The 2025 data in this report shows them operating at a volume that makes them primary attack surfaces. Start with whichever category above matches your biggest gap.
Book a demo to see your organization’s exposure across every category in this report.
